Threat actors misuse OAuth applications to automate financially driven attacks
Microsoft Threat Intelligence presents cases of threat actors misusing OAuth applications as automation tools in financially motivated attacks.
Much of cybercrime today is fueled by underground markets where malware and cybercriminal services are available for purchase. These markets in the deep web commoditize malware operations. Even novice cybercriminals can buy malware toolkits and other services they might need for malware campaigns: encryption, hosting, antimalware evasion, spamming, and many others.
Hawkeye Keylogger is an info-stealing malware that’s being sold as malware-as-a-service. Over the years, the malware authors behind Hawkeye have improved the malware service, adding new capabilities and techniques. It was last used in a high-volume campaign in 2016.
This year marked the resurgence of Hawkeye. In April, malware authors started peddling a new version of the malware that they called Hawkeye Keylogger – Reborn v8. Not long after, on April 30, Office 365 Advanced Threat Protection (Office 365 ATP) detected a high-volume campaign that distributed the latest variants of this keylogger.
At the onset, Office 365 ATP blocked the email campaign and protected customers, 52% of whom are in the software and tech sector. Companies in the banking (11%), energy (8%), chemical (5%), and automotive (5%) industries are also among the top targets
 Figure 1. Top industries targeted by the April 2018 Hawkeye campaign
Figure 1. Top industries targeted by the April 2018 Hawkeye campaign
Office 365 ATP uses intelligent systems that inspect attachments and links for malicious content to protect customers against threats like Hawkeye in real time. These automated systems include a robust detonation platform, heuristics, and machine learning models. Office 365 ATP uses intelligence from various sensors, including multiple capabilities in Windows Defender Advanced Threat Protection (Windows Defender ATP).
Windows Defender AV (a component of Windows Defender ATP) detected and blocked the malicious attachments used in the campaign in at least 40 countries. United Arab Emirates accounted for 19% of these file encounters, while the Netherlands (15%), the US (11%), South Africa (6%) and the UK (5%) make the rest of the top 5 countries that saw the lure documents used in the campaign. A combination of generic and heuristic protections in Windows Defender AV (TrojanDownloader:O97M/Donoff, Trojan:Win32/Tiggre!rfn, Trojan:Win32/Bluteal!rfn, VirTool:MSIL/NetInject.A) ensured these threats are blocked in customer environments.
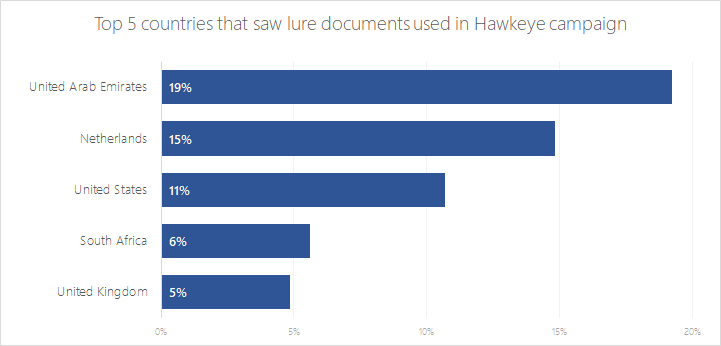
Figure 2. Top countries that encountered malicious documents used in the Hawkeye campaign
As part of our job to protect customers from malware attacks, Office 365 ATP researchers monitor malware campaigns like Hawkeye and other developments in the cybercriminal landscape. Our in-depth investigation into malware campaigns like Hawkeye and many others adds to the vast threat intelligence we get from the Microsoft Intelligent Security Graph, which enables us to continuously raise the bar in security. Through the Intelligent Security Graph, security technologies in Microsoft 365 share signals and detections, allowing these technologies to automatically update protection and detection mechanisms, as well as orchestrate remediation across Microsoft 365.
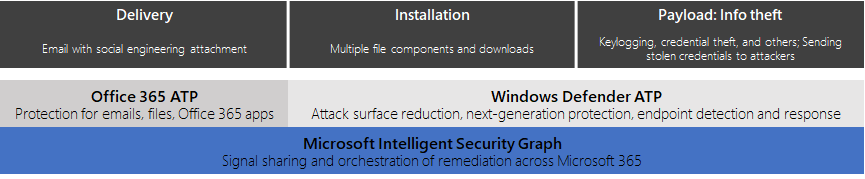
Figure 3. Microsoft 365 threat protection against Hawkeye
Despite its name, Hawkeye Keylogger – Reborn v8 is more than a common keylogger. Over time, its authors have integrated various modules that provide advanced functionalities like stealth and detection evasion, as well as credential theft and more.
Malware services like Hawkeye are advertised and sold in the deep web, which requires anonymity networks like Tor to access, etc. Interestingly, the Hawkeye authors advertised their malware and even published tutorial videos on a website on the surface web (that has since been taken down). Even more interesting, based on underground forums, it appears the malware authors have employed intermediary resellers, an example of how cybercriminal underground business models expand and evolve.
 Our investigation into the April 2018 Hawkeye campaign shows that the cybercriminals have been preparing for the operation since February, when they registered the domains they later used in the campaign.
Our investigation into the April 2018 Hawkeye campaign shows that the cybercriminals have been preparing for the operation since February, when they registered the domains they later used in the campaign.
Typical of malware campaigns, the cybercriminals undertook the following steps:
Like other malware toolkits, Hawkeye comes with an admin panel that cybercriminals use to monitor and control the attack.

Figure 4: Hawkeye’s admin panel
Interestingly, some of the methods used in this Hawkeye campaign are consistent with previous attacks. This suggests that the cybercriminals behind this campaign may be the same group responsible for malware operations that delivered the remote access tool (RAT) Remcos and the info-stealing bot malware Loki. The following methods were used in these campaigns:
In late April, Office 365 ATP analysts spotted a new spam campaign with the subject line RFQ-GHFD456 ADCO 5647 deadline 7th May carrying a Word document attachment named Scan Copy 001.doc. While the attachment’s file name extension was .doc, it was in fact a malicious Office Open XML format document, which usually uses a .docx file name extension.
In total, the campaign used four different subject lines and five attachments.


Figure 5: Sample emails used in the Hawkeye campaign
Because the attachment contains malicious code, Microsoft Word opens with a security warning. The document uses a common social engineering lure: it displays a fake message and an instruction to “Enable editing” and “Enable content”.

Figure 6: The malicious document with social engineering lure
The document contains an embedded frame that connects to a remote location using a shortened URL.

Figure 7: frame in settings.rels.xml on the document
The frame loads an .rtf file from hxxp://bit[.]ly/Loadingwaitplez, which redirects to hxxp://stevemike-fireforce[.]info/work/doc/10.doc.

Figure 8: RTF loaded as a frame inside malicious document
The RTF has an embedded malicious .xlsx file with macro as an OLE object, which in turn contains a stream named PACKAGE that contains the .xlsx contents.
The macro script is mostly obfuscated, but the URL to the malware payload is notably in plaintext.

Figure 9: Obfuscated macro entry point
De-obfuscating the entire script makes its intention clear. The first section uses PowerShell and the System.Net.WebClient object to download the malware to the path C:\Users\Public\svchost32.exe and execute it.
The macro script then terminates both winword.exe and excel.exe. In specific scenarios where Microsoft Word overrides default settings and is running with administrator privileges, the macro can delete Windows Defender AV’s malware definitions. It then changes the registry to disable Microsoft Office’s security warnings and safety features.
In summary, the campaign’s delivery comprises of multiple layers of components that aim to evade detection and possibly complicate analysis by researchers.
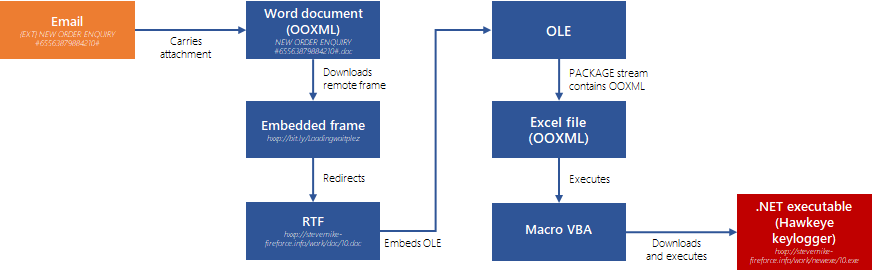 Figure 10: The campaign’s delivery stages
Figure 10: The campaign’s delivery stages
The downloaded payload, svchost32.exe, is a .NET assembly named Millionare that is obfuscated using a custom version of ConfuserEx, a well-known open-source .NET obfuscator.
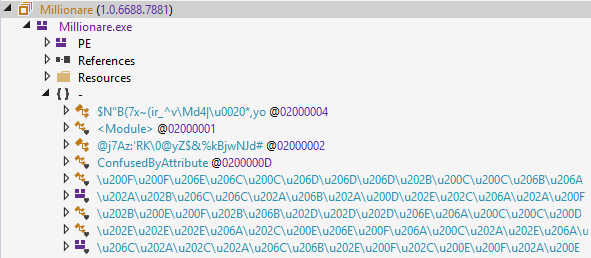 Figure 11: Obfuscated .NET assembly Millionare showing some of the scrambled names
Figure 11: Obfuscated .NET assembly Millionare showing some of the scrambled names
The obfuscation modifies the .NET assembly’s metadata such that all the class and variable names are non-meaningful and scrambled names in Unicode. This obfuscation causes some analysis tools like .NET Reflector to show some namespaces or classes names as blank, or in some cases, display parts of the code backwards.

Figure 12: .NET Reflector presenting the code backwards due to obfuscation
Finally, the .NET binary loads an unpacked .NET assembly, which includes DLL files embedded as resources in the portable executable (PE).

Figure 13: Loading the unpacked .NET assembly during run-time
The DLL that initiates the malicious behavior is embedded as a resource in the unpacked .NET assembly. It is loaded in memory using process hollowing, a code injection technique that involves spawning a new instance of a legitimate process and then “hollowing it out”, i.e., replacing the legitimate code with malware.

Figure 14: In-memory unpacking of the malware using process hollowing.
Unlike previous Hawkeye variants (v7), which loaded the main payload into its own process, the new Hawkeye malware injects its code into MSBuild.exe, RegAsm.exe, and VBC.exe, which are signed executables that ship with .NET framework. This is an attempt to masquerade as a legitimate process.

Figure 15: Obfuscated calls using .NET reflection to perform process hollowing injection routine that injects the malware’s main payload into RegAsm.exe
Additionally, in the previous version, the process hollowing routine was written in C. In the new version, this routine is completely rewritten as a managed .NET that calls the native Windows API.

Figure 16: Process hollowing routine implemented in .NET using native API function calls
The new Hawkeye variants created by the latest version of the malware toolkit have multiple sophisticated functions for information theft and evading detection and analysis.
The main keylogger functionality is implemented using hooks that monitor key presses, as well as mouse clicks and window context, along with clipboard hooks and screenshot capability.
It has specific modules for extracting and stealing credentials from the following applications:
Like many other malware campaigns, it uses the legitimate BrowserPassView and MailPassView tools to dump credentials from the browser and email client. It also has modules for taking screenshots of the desktop, as well as the webcam, if it exists.
Notably, the malware has a mechanism to visit certain URLs for click-based monetization.
On top of the processes hollowing technique, this malware uses other methods for stealth, including alternate data streams that remove mark of the web (MOTW) from the malware’s downloaded files.
This malware can be configured to delay execution by any number of seconds, a technique used mainly to avoid detection by various sandboxes.
It prevents antivirus software from running using an interesting technique. It adds keys to the registry location HKLM\Software\Windows NT\Current Version\Image File Execution Options and sets the Debugger value for certain processes to rundll32.exe, which prevents execution. It targets the following processes related to antivirus and other security software:
Further, it blocks access to certain domains that are usually associated with antivirus or security updates. It does this by modifying the HOSTS file. The list of domains to be blocked is determined by the attacker using a config file.
This malware protects its own processes. It blocks the command prompt, registry editor, and task manager. It does this by modifying registry keys for local group policy administrative templates. It also constantly checks active windows and renders action buttons unusable if the window title matches “ProcessHacker”, “Process Explorer”, or “Taskmgr”.
Meanwhile, it prevents other malware from infecting the machine. It repeatedly scans and removes any new values to certain registry keys, stops associated processes, and deletes related files.
Hawkeye attempts to avoid automated analysis. The delay in execution is designed to defeat automated sandbox analysis that allots only a certain time for malware execution and analysis. It likewise attempts to evade manual analysis by monitoring windows and exiting when it finds the following analysis tools:
Hawkeye illustrates the continuous evolution of malware in a threat landscape fueled by the cybercriminal underground. Malware services make malware accessible to even unsophisticated operators, while simultaneously making malware more durable with advanced techniques like in-memory unpacking and abuse of .NET’s CLR engine for stealth. In this blog we covered the capabilities of its latest version, Hawkeye Keylogger – Reborn v8, highlighting some of the enhancements from the previous version. Given its history, Hawkeye is likely to release a new version in the future.
Organizations should continue educating their employees about spotting and preventing social engineering attacks. After all, Hawkeye’s complicated infection chain begins with a social engineering email and lure document. A security-aware workforce will go a long way in securing networks against attacks.
More importantly, securing mailboxes, endpoints, and networks using advanced threat protection technologies can prevent attacks like Hawkeye, other malware operations, and sophisticated cyberattacks.
Our in-depth analysis of the latest version and our insight into the cybercriminal operation that drives this development allow us to proactively build robust protections against both known and unknown threats.
Office 365 Advanced Threat Protection (Office 365 ATP) protects mailboxes as well as files, online storage, and applications from malware campaigns like Hawkeye. It uses a robust detonation platform, heuristics, and machine learning to inspect attachments and links for malicious content in real-time, ensuring that emails that carry Hawkeye and other threats don’t reach mailboxes and devices. Learn how to add Office 365 ATP to existing Exchange or Office 365 plans.
Windows Defender Antivirus (Windows Defender AV) provides an additional layer of protection by detecting malware delivered through email, as well as other infection vectors. Using local and cloud-based machine learning, Windows Defender AV’s next-gen protection can block even new and unknown threats on Windows 10 and Windows 10 in S mode.
Additionally, endpoint detection and response (EDR) capabilities in Windows Defender Advanced Threat Protection (Windows Defender ATP) expose sophisticated and evasive malicious behavior, such as those used by Hawkeye. Sign up for free Windows Defender ATP trial.
Windows Defender ATP’s rich detection libraries are powered by machine learning and allows security operations teams to detect and respond to anomalous attacks in the network. For example, machine learning detection algorithms surface the following alert when Hawkeye uses a malicious PowerShell to download the payload:

Figure 16: Windows Defender ATP alert for Hawkeye’s malicious PowerShell component
Windows Defender ATP also has behavior-based machine learning algorithms that detect the payload itself:

Figure 17: Windows Defender ATP alert for Hawkeye’s payload
These security technologies are part of the advanced threat protection solutions in Microsoft 365. Enhanced signal sharing across services in Windows, Office 365, and Enterprise Mobility + Security through the Microsoft Intelligent Security Graph enables the automatic update of protections and orchestration of remediation across Microsoft 365.
Office 365 ATP Research
Files (SHA-256)
*Updated 07/12/18 (Removed statement that Hawkeye Keylogger is also known as iSpy Keylogger
Questions, concerns, or insights on this story? Join discussions at the Microsoft community and Windows Defender Security Intelligence.
Follow us on Twitter @WDSecurity and Facebook Windows Defender Security Intelligence.