Using Azure Active Directory groups to manage a user’s app and data access
Applies to Dynamics 365 for Customer Engagement apps version 9.x
Applies to Common Data Service
The administration of app and data access for Microsoft Dynamics 365 for Customer Engagement and Common Data Service has been extended to allow administrators to use their organization’s Azure Active Directory (Azure AD) groups to manage access rights for licensed Customer Engagement and Common Data Service users.
Both types of Azure AD groups—Office and Security—can be used to secure user-access rights. Using groups lets administrators assign a security role with its respective privileges to all the members of the group, instead of having to provide the access rights to an individual team member.
The administrator can create Azure AD group teams that are associated to the Azure AD groups in each of the Customer Engagement and Common Data Service environments and assign a security role to these group teams. When members of these group teams access these environments, their access rights are automatically granted based on the group team’s security role.
Provision and deprovision users
Once the group team and its security role is established in an environment, user access to the environment is based on the user membership of the Azure AD groups. When a new user is created in the tenant, all the administrator needs to do is assign the user to the appropriate Azure AD group, and assign Customer Engagement and Common Data Service licenses. The user can immediately access the environment without the need to wait for the administrator to assign a security role.
When users are deleted/disabled in Azure AD or removed from the Azure AD groups, they lose their group membership and won’t be able to access the environment when they try to sign in.
Remove user access at run time
When a user is removed from the Azure AD groups by an administrator, the user is removed from the group team, and they lose their access rights the next time they access the environment. The memberships for the user’s Azure AD groups and Customer Engagement group teams are synchronized, and the user’s access rights are dynamically derived at run time.
Administer user security role
Administrators no longer have to wait for the user to sync to the environment and then to assign a security role to the user individually by using Azure AD group teams. Once a group team is established and created in an environment with a security role, any licensed Customer Engagement and Common Data Service users who are added to the Azure AD group can immediately access the environment.
Lock down user access to environments
Administrators can continue to use an Azure AD security group to lock down the list of users synced to an environment. This can be further reinforced by using Azure AD group teams. To lock down environment or app access to restricted environments, the administrator can create separate Azure AD groups for each environment and assign the appropriate security role for these groups. Only these Azure AD group team members have the access rights to the environment.
Share PowerApps to team members of Azure AD group
When canvas and model-driven apps are shared to an Azure AD group team, team members can immediately run the apps.
User-owned and team-owned records
A new property has been added to the security role definition to provide special team privileges when the role is assigned to group teams. This type of security role allows team members to be granted User/Basic-level privileges as if the security role is directly assigned to them. Team members can create and be an owner of records without the need to have an additional security role assigned.
A group team can own one or more records. To make a team an owner of the record, you must assign the record to the team.
While teams provide access to a group of users, you must still associate individual users with security roles that grant the privileges that they need to create, update, or delete user-owned records. These privileges can’t be applied by assigning a nonmember’s privilege inherited security role to a team and then adding the user to that team. If you need to provide your team members the team privileges directly, without their own security role, you can assign the team a security role that has member’s privilege inheritance.
Availability
These enhancements will be released regionally in the next few weeks. To check if your environment has been enabled to use Azure AD groups, follow these steps:
1. Go to Settings > Security.
2. Select Teams.
3. Open the View drop-down list.
If the AAD Office Group Teams and AAD Security Group Teams are listed, then your environment is enabled.
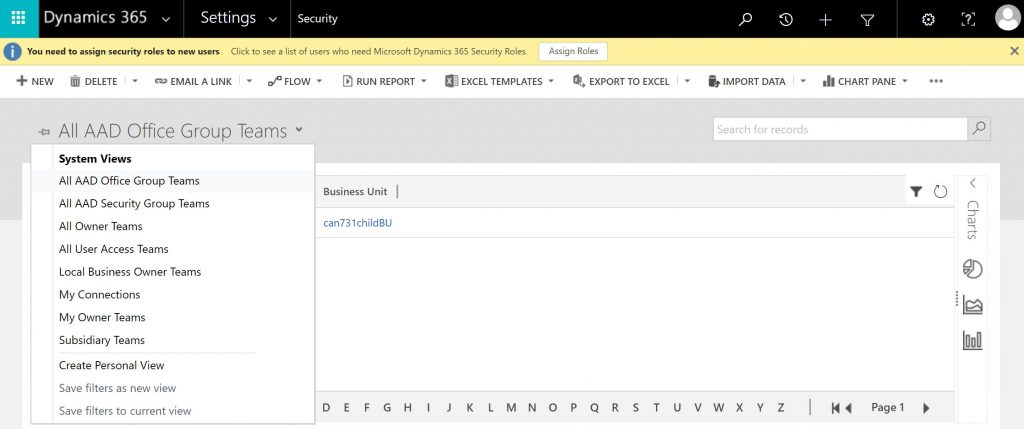
Teams System Views
For detailed information, see
Team Member’s privilege inheritance, About Group teams, and
Manage app and resource access using Azure Active Directory groups


