Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity Blog
- Conditional Access for SharePoint Online with Microsoft Intune
Conditional Access for SharePoint Online with Microsoft Intune
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
By
Published
Sep 08 2018 06:09 AM
6,645
Views
Sep 08 2018
06:09 AM
Sep 08 2018
06:09 AM
First published on CloudBlogs on Mar 05, 2015
As part of a recent service update to Microsoft Intune, the Intune team announced that organizations now have the ability to control access to SharePoint Online from Office Mobile apps on Android devices and OneDrive apps for iOS and Android devices. With this feature, you can restrict access to SharePoint Online to only those users who have enrolled their devices in management with Microsoft Intune and are compliant with IT policy. This becomes important for many organizations who are migrating to Office 365 as a means to ensure that data is protected. This blog post describes how this feature works in detail. Step 2: Configure the SharePoint Online policy
Now you need to tell SharePoint Online that you wish to enforce conditional access. This is done by configuring the SharePoint Online policy in the Intune admin console, which configures a policy in Azure Active Directory to require that only managed and compliant devices may access SharePoint Online through supported OneDrive mobile apps.
You must also specify which Azure Active Directory security groups will be subjected to this policy. If you need to configure your security groups you can do so in either the
Office 365 admin center
or the
Intune account portal.
Additionally, you may specify security groups that should be exempted from this policy. This is an optional step, however it is recommended if you have particular users who may fall in to one of your targeted security groups who you do not want to be blocked.
Once this policy is configured, users who belong to any of the targeted groups will be required to enroll their device with Intune in order to access SharePoint Online. Additionally, those users’ devices must be compliant with any deployed compliance policies. Note that the targeting for compliance policies is against Intune groups, whereas targeting for conditional access policies is against Azure Active Directory security groups.
To configure the SharePoint Online conditional access policy, go to Policy > Conditional Access > SharePoint Online Policy. Specify the applicable Azure Active Directory security groups you want under the Targeted Groups section, and (optionally) specify security groups under the Exempted Groups section.
Step 2: Configure the SharePoint Online policy
Now you need to tell SharePoint Online that you wish to enforce conditional access. This is done by configuring the SharePoint Online policy in the Intune admin console, which configures a policy in Azure Active Directory to require that only managed and compliant devices may access SharePoint Online through supported OneDrive mobile apps.
You must also specify which Azure Active Directory security groups will be subjected to this policy. If you need to configure your security groups you can do so in either the
Office 365 admin center
or the
Intune account portal.
Additionally, you may specify security groups that should be exempted from this policy. This is an optional step, however it is recommended if you have particular users who may fall in to one of your targeted security groups who you do not want to be blocked.
Once this policy is configured, users who belong to any of the targeted groups will be required to enroll their device with Intune in order to access SharePoint Online. Additionally, those users’ devices must be compliant with any deployed compliance policies. Note that the targeting for compliance policies is against Intune groups, whereas targeting for conditional access policies is against Azure Active Directory security groups.
To configure the SharePoint Online conditional access policy, go to Policy > Conditional Access > SharePoint Online Policy. Specify the applicable Azure Active Directory security groups you want under the Targeted Groups section, and (optionally) specify security groups under the Exempted Groups section.

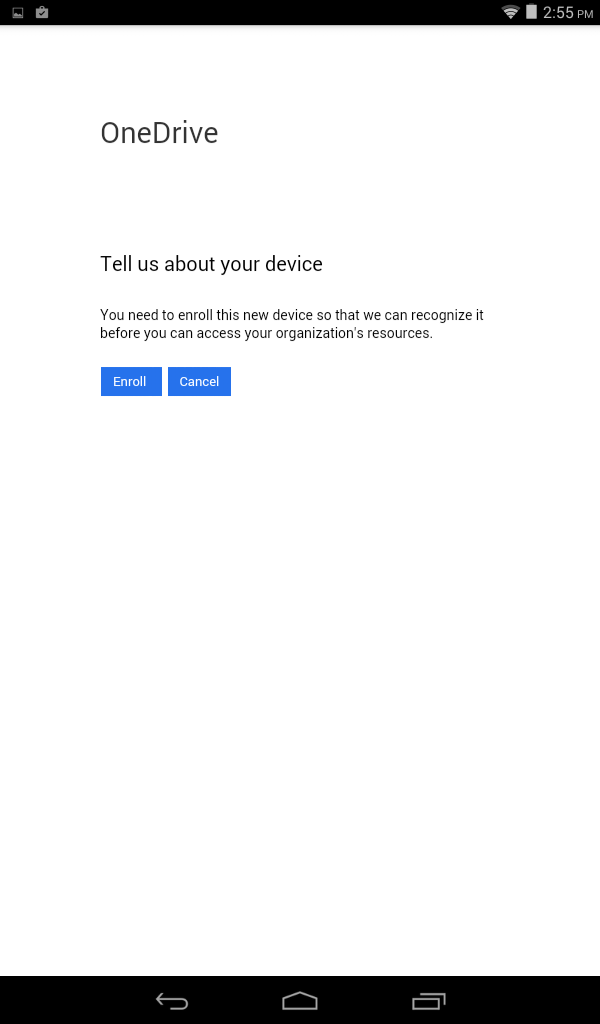 When the user clicks "Enroll" they are redirected to the Intune Company Portal app in the Apple App Store or Google Play. Once installed, the Company Portal app walks the user through the enrollment process.
After enrolling, Intune will evaluate the device against the Compliance Policy that was deployed in Step 1. If any compliance issues are found, the user will then be shown a different message in OneDrive:
When the user clicks "Enroll" they are redirected to the Intune Company Portal app in the Apple App Store or Google Play. Once installed, the Company Portal app walks the user through the enrollment process.
After enrolling, Intune will evaluate the device against the Compliance Policy that was deployed in Step 1. If any compliance issues are found, the user will then be shown a different message in OneDrive:
 From here, the user is redirected to the Intune web portal they will see a list of compliance issues that Intune has identified based on the Compliance Policy that was deployed. The user can then view more details on how to remediate the issue using the “How to resolve this” link. Once the issue is remediated, the user must trigger another Intune policy evaluation by clicking the Check Compliance button.
From here, the user is redirected to the Intune web portal they will see a list of compliance issues that Intune has identified based on the Compliance Policy that was deployed. The user can then view more details on how to remediate the issue using the “How to resolve this” link. Once the issue is remediated, the user must trigger another Intune policy evaluation by clicking the Check Compliance button.
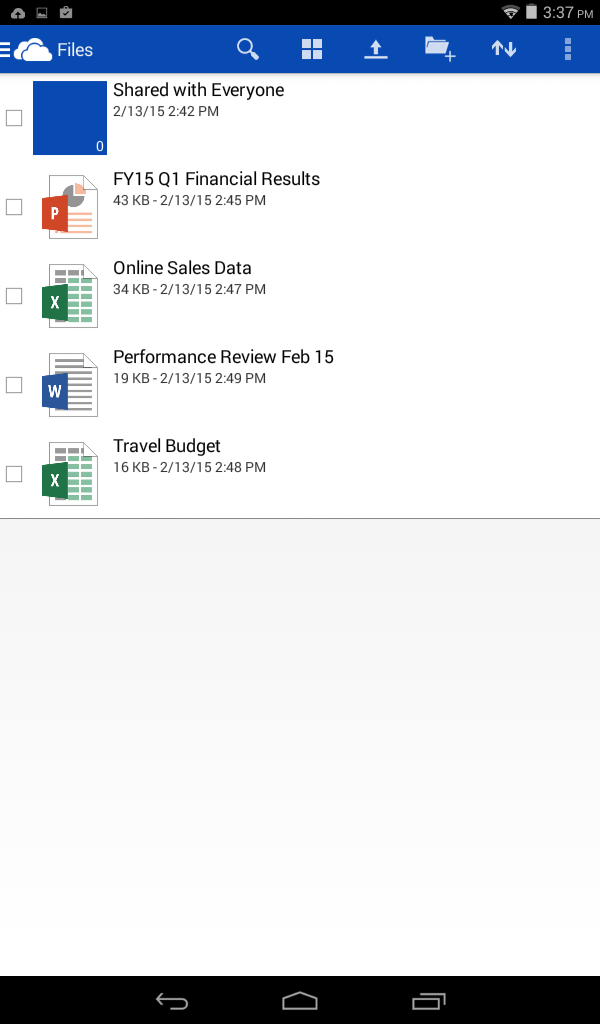
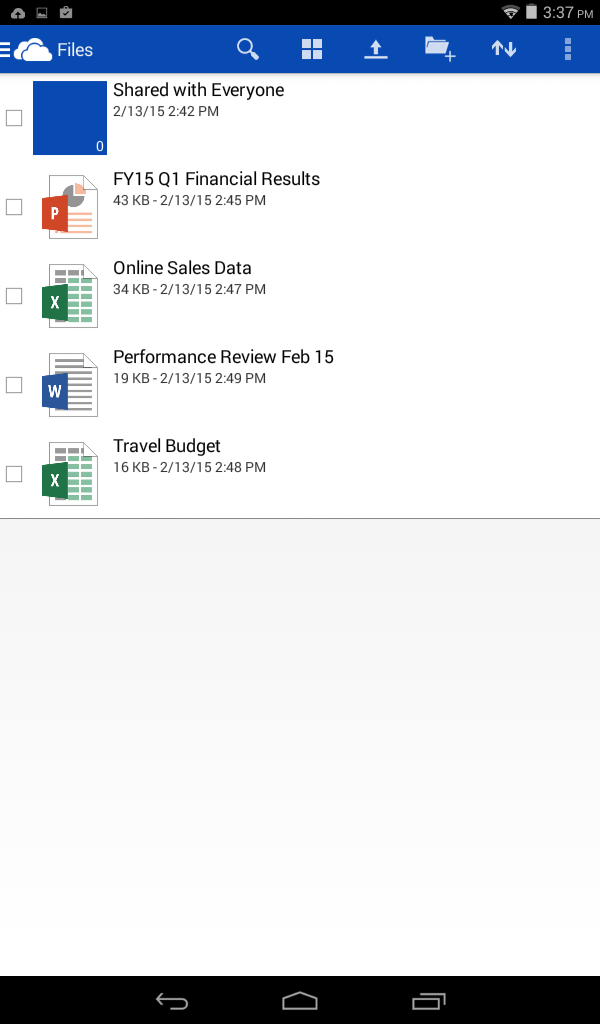
 Once the user’s device is enrolled, registered with Azure Active Directory, and compliant with all Compliance Policies, the user will then be allowed access to their OneDrive for Business work files.
Once the user’s device is enrolled, registered with Azure Active Directory, and compliant with all Compliance Policies, the user will then be allowed access to their OneDrive for Business work files.
As part of a recent service update to Microsoft Intune, the Intune team announced that organizations now have the ability to control access to SharePoint Online from Office Mobile apps on Android devices and OneDrive apps for iOS and Android devices. With this feature, you can restrict access to SharePoint Online to only those users who have enrolled their devices in management with Microsoft Intune and are compliant with IT policy. This becomes important for many organizations who are migrating to Office 365 as a means to ensure that data is protected. This blog post describes how this feature works in detail.
How the solution works
OneDrive mobile applications attempting to access OneDrive for Business files hosted on SharePoint Online will be evaluated for two basic properties:- Is the device managed and registered with Azure Active Directory?
- Is the device compliant?
Deploying the solution
Deploying the SharePoint Online conditional access feature boils down to two fundamental steps: Step 1: Define and deploy a compliance policy A compliance policy defines what it means for a device to be compliant in order to access SharePoint Online. Intune will compute whether a device meets these criteria and will then set a property in Azure Active Directory, which is then used later when authorizing access. We have separated this from Configuration Policies (security settings and resource access profiles) in order to make it super clear as to what rules will actually result in a user getting blocked from their work files. A compliance policy can require that a device have passcode settings applied, encryption enabled, not be jailbroken or rooted, and to have an email profile managed by Intune. If a device is capable of remediating a setting, it will, however if auto-remediation is not possible then the device will be marked as not compliant and it will be blocked from SharePoint Online until the user remediates the issue. Full details about each of these rules can be found in this TechNet article . To create a Compliance Policy in the Intune console, go to Policy > Compliance Policies and select Add… Then select the settings you require, and click Save Policy. You will then be prompted to deploy to user or device groups. Step 2: Configure the SharePoint Online policy
Now you need to tell SharePoint Online that you wish to enforce conditional access. This is done by configuring the SharePoint Online policy in the Intune admin console, which configures a policy in Azure Active Directory to require that only managed and compliant devices may access SharePoint Online through supported OneDrive mobile apps.
You must also specify which Azure Active Directory security groups will be subjected to this policy. If you need to configure your security groups you can do so in either the
Office 365 admin center
or the
Intune account portal.
Additionally, you may specify security groups that should be exempted from this policy. This is an optional step, however it is recommended if you have particular users who may fall in to one of your targeted security groups who you do not want to be blocked.
Once this policy is configured, users who belong to any of the targeted groups will be required to enroll their device with Intune in order to access SharePoint Online. Additionally, those users’ devices must be compliant with any deployed compliance policies. Note that the targeting for compliance policies is against Intune groups, whereas targeting for conditional access policies is against Azure Active Directory security groups.
To configure the SharePoint Online conditional access policy, go to Policy > Conditional Access > SharePoint Online Policy. Specify the applicable Azure Active Directory security groups you want under the Targeted Groups section, and (optionally) specify security groups under the Exempted Groups section.
Step 2: Configure the SharePoint Online policy
Now you need to tell SharePoint Online that you wish to enforce conditional access. This is done by configuring the SharePoint Online policy in the Intune admin console, which configures a policy in Azure Active Directory to require that only managed and compliant devices may access SharePoint Online through supported OneDrive mobile apps.
You must also specify which Azure Active Directory security groups will be subjected to this policy. If you need to configure your security groups you can do so in either the
Office 365 admin center
or the
Intune account portal.
Additionally, you may specify security groups that should be exempted from this policy. This is an optional step, however it is recommended if you have particular users who may fall in to one of your targeted security groups who you do not want to be blocked.
Once this policy is configured, users who belong to any of the targeted groups will be required to enroll their device with Intune in order to access SharePoint Online. Additionally, those users’ devices must be compliant with any deployed compliance policies. Note that the targeting for compliance policies is against Intune groups, whereas targeting for conditional access policies is against Azure Active Directory security groups.
To configure the SharePoint Online conditional access policy, go to Policy > Conditional Access > SharePoint Online Policy. Specify the applicable Azure Active Directory security groups you want under the Targeted Groups section, and (optionally) specify security groups under the Exempted Groups section.

End user experience
Once the above steps are in place, users belonging to the security groups specified in the SharePoint Online conditional access policy will start getting blocked from accessing work files in OneDrive apps for Android and iOS. Users will see a message after they log in telling them that they must enroll with Intune. Here is an example on Android: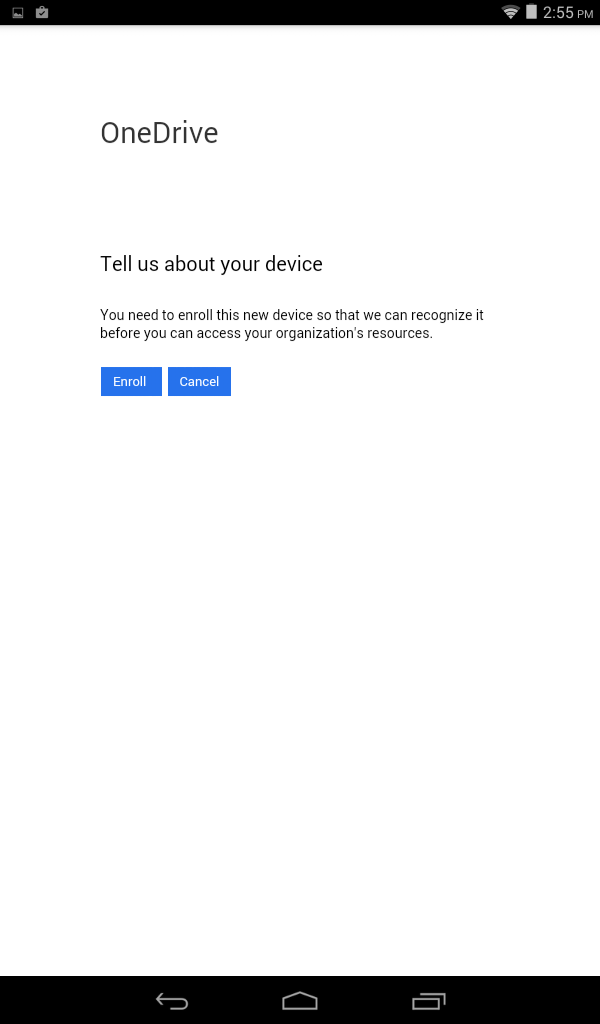 When the user clicks "Enroll" they are redirected to the Intune Company Portal app in the Apple App Store or Google Play. Once installed, the Company Portal app walks the user through the enrollment process.
After enrolling, Intune will evaluate the device against the Compliance Policy that was deployed in Step 1. If any compliance issues are found, the user will then be shown a different message in OneDrive:
When the user clicks "Enroll" they are redirected to the Intune Company Portal app in the Apple App Store or Google Play. Once installed, the Company Portal app walks the user through the enrollment process.
After enrolling, Intune will evaluate the device against the Compliance Policy that was deployed in Step 1. If any compliance issues are found, the user will then be shown a different message in OneDrive:
 From here, the user is redirected to the Intune web portal they will see a list of compliance issues that Intune has identified based on the Compliance Policy that was deployed. The user can then view more details on how to remediate the issue using the “How to resolve this” link. Once the issue is remediated, the user must trigger another Intune policy evaluation by clicking the Check Compliance button.
From here, the user is redirected to the Intune web portal they will see a list of compliance issues that Intune has identified based on the Compliance Policy that was deployed. The user can then view more details on how to remediate the issue using the “How to resolve this” link. Once the issue is remediated, the user must trigger another Intune policy evaluation by clicking the Check Compliance button.
 Once the user’s device is enrolled, registered with Azure Active Directory, and compliant with all Compliance Policies, the user will then be allowed access to their OneDrive for Business work files.
Once the user’s device is enrolled, registered with Azure Active Directory, and compliant with all Compliance Policies, the user will then be allowed access to their OneDrive for Business work files.
Additional resources
For additional technical resources on Conditional Access in Microsoft Intune, visit TechNet here . - Chris Green, Senior Program Manager
0
Likes
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.