Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Home
- Security, Compliance, and Identity
- Microsoft Entra Blog
- Azure AD Application Proxy now supports custom domain names!
Azure AD Application Proxy now supports custom domain names!
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Published
Sep 06 2018 08:06 PM
3,276
Views
Sep 06 2018
08:06 PM
Sep 06 2018
08:06 PM
First published on CloudBlogs on Apr, 22 2015
Howdy folks, One of our big learnings over the past 90 days has been that customer interest in using our Azure AD App Proxy is far greater than we anticipated. This is a nice problem to have and we're excited to see such fast adoption. In addition to helping customers go live with the service, our app proxy team has learned a ton from customers and has been hard at work improving the service including things like:
Howdy folks, One of our big learnings over the past 90 days has been that customer interest in using our Azure AD App Proxy is far greater than we anticipated. This is a nice problem to have and we're excited to see such fast adoption. In addition to helping customers go live with the service, our app proxy team has learned a ton from customers and has been hard at work improving the service including things like:
- Improving our SharePoint experience
- Support NDES publishing for Intune clients
- Enable publishing only specified paths to the backend server
- Checking connector status from the cloud
- Conditional access with MFA
The Azure AD App Proxy now supports publishing applications using custom domain names!
This has been the single biggest request from customers and we're excited to make it available. Up until today, every application is published under a domain name that is provided and maintained by us: msappproxy.net. We take care of the certificates and DNS records for this domain. Your application is instantly published, securely in high scale and high availability guarantied. We are going to keep this quick and robust experience going forward. But, many customers want to be able to use their own domain name for published applications. The main benefit of custom domains is that your employees, partners and customers will now see branded URLs that looks familiar to them. This new capability also enables existing apps to seamlessly work with the same URLs both internally and externally. This will solve many application compatibility problems and will make all links work all the time. For example, let's consider collaboration site with its internal and external URLs being https://docs.contoso.com/ . If an employee is accessing it from your corporate network, the internal DNS will route him directly to this server. If the employee is working at a Starbucks, the public DNS will direct them to Azure AD Application Proxy which, after authentication and authorization, will let them access this app with an SSO experience. This also means that if a user receives an email or notification with embedded link to a document on that site (e.g. https://docs.contoso.com/2015budget.aspx ), the link will work in either location. To use a custom domain here's what you do:-
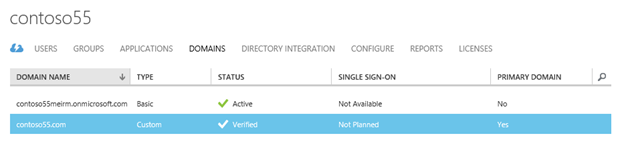
Verify the parent domain (e.g. contoso55.com) using the "domains" tab in the directory configuration. It will require you to add a record for your domains to proof ownership.
-
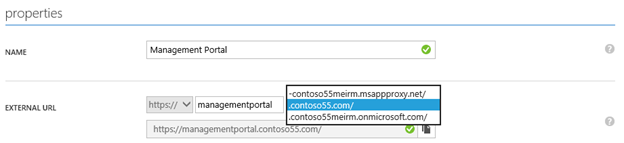
From the application's configure page, select this parent domain name and select the exact parent domain to be used (e.g. app1.contoso55.com)
- Save the application to continue configuring.
-
Upload a certificate that matches this domain name in PFX file format. The certificate must be a valid certificate that has a private key. Simple certificates, SAN or wildcard certificates can be used. Each time you upload a new certificate, we bound the application's host to the new one.
-
Add to the public DNS that cover this domain name a CNAME record that would point to the msappproxy.net record of your application as instructed in the UI:
0
Likes
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.