Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Home
- Security, Compliance, and Identity
- Microsoft Entra Blog
- Azure AD and Microsoft Identity Manager Reporting – we’ve gone hybrid!
Azure AD and Microsoft Identity Manager Reporting – we’ve gone hybrid!
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Published
Sep 06 2018 08:13 PM
1,629
Views
Sep 06 2018
08:13 PM
Sep 06 2018
08:13 PM
First published on CloudBlogs on May, 22 2015
Howdy folks, I've got one more thing to share with you this week before the long Memorial Day holiday here in the U.S. One of the things that really differentiates Microsoft from the rest of the enterprise cloud vendors is our deep belief in the hybrid enterprise. We know that every company of any size will have IT investments on premises and in the cloud for the foreseeable future. And we know that our customers need efficient, cost effective tools that let them get the most of both their cloud and on-premises investments. So today, I'm happy to tell you about the next step in our hybrid journey. We've just turned on the first set of hybrid reports in Azure AD. These reports give customers visibility into both Azure AD in the cloud and Microsoft Identity Manager (MIM) on-premises activity in these areas:
Howdy folks, I've got one more thing to share with you this week before the long Memorial Day holiday here in the U.S. One of the things that really differentiates Microsoft from the rest of the enterprise cloud vendors is our deep belief in the hybrid enterprise. We know that every company of any size will have IT investments on premises and in the cloud for the foreseeable future. And we know that our customers need efficient, cost effective tools that let them get the most of both their cloud and on-premises investments. So today, I'm happy to tell you about the next step in our hybrid journey. We've just turned on the first set of hybrid reports in Azure AD. These reports give customers visibility into both Azure AD in the cloud and Microsoft Identity Manager (MIM) on-premises activity in these areas:
- Self Service Password Registration
- Self Service Password Reset
- Self Service Group Management
- Your visibility is unified: Single pane of glass to track identity management activities across your infrastructures, unlocking further business insights from your data!
- Your operational cost is dramatically reduced: Eliminating the need for deploying and operating complex on-premises reporting data warehouse and analytics!
- Your data is yours: Exporting and customizing reporting data is now easy, by capturing (or forwarding) Identity Manager reporting data from the standard Windows Event Log. This can be used to generate custom reports, or forward to a SIEM system, for example.
Which hybrid reports are available today?
With Hybrid Reports, Azure AD can display unified identity management activity reports. The data originates from Azure AD itself, and from the on-premises Microsoft Identity Manager 2016 (which is in beta these days, going through final testing before the final release). For example, if you want to know who registered to self-service password reset (SSPR) in the last month, you can see it all in Azure AD management portal. In this report you will see users who registered to SSPR both from within the access panel (myapps.microsoft.com) and from Identity Manager. We are hearing from customers that the following three reports are the highest priority to go hybrid: SSPR registration activity , SSPR reset activity , and group activity . So today's preview covers these three reports.

Figure 1: Hybrid Report for Group Activity
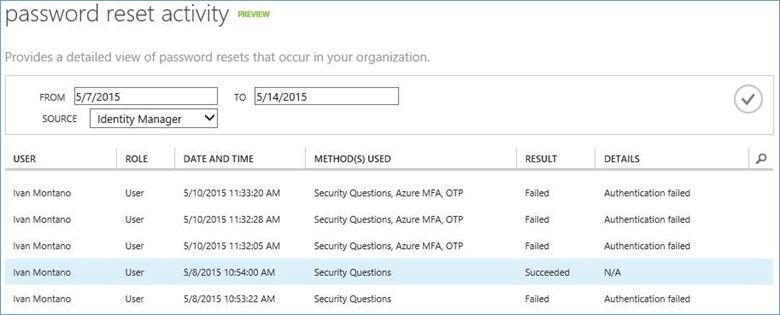
Figure 2: Hybrid Report for Password Reset Activity

Figure 3: Hybrid Report for Password Reset Registration Activity
How to start using Hybrid Reports?
You need to download and install a connector (a.k.a. reporting agent) to hook up Microsoft Identity Manager 2016 (beta) with Azure AD reports. This connector uploads data from service requests in Identity Manager, to your tenant's reports. With this connector, you do not need to install the traditional on-premises Identity Manager reporting component infrastructure. You can download the connector package from the Azure AD Configuration page, similar to other Azure AD connectors. The download contains a ZIP file with the connector and your certificate, used to authenticate to your tenant in the cloud. Copy the downloaded ZIP file to the server running Microsoft Identity Manager, install the connector by running it and accepting the license agreement, and restart Identity Manager. You are done!

Figure 4: Download of the Hybrid Reports connector
You can start viewing the reporting data in the familiar Azure AD reports page. For now, you should toggle between the data sources (Azure AD or Identity Manager) using the drop-down list box showed in the images above. Going forward, we plan to eliminate the drop-down box, and merge the data onto a single report. If you want to turn off the uploading of reporting data from Identity Manager, you can do this in the configuration file, located in your Identity Manager installation folder. For example: C:Program FilesMicrosoft Forefront Identity Manager2010ServiceMicrosoft.ResourceManagement.Service.exe.config . Find the configuration setting as follows:<resourceManagementService hybridReportingRequestLoggingEnabled="true"/>
And set its value to "false". Save the file and restart Identity Manager. You are done.How does it work? And how can you customize the usage of reporting data?

Figure 5: Schematic data flow from Identity Manager to Azure AD
The Identity Manager emits activity data to the Windows Event Log, in a well-defined path: Application and Services LogsIdentity Manager Request Log . The connector performs some processing of the events and uploads to Azure. In Azure, the activity data is stored together with your Azure AD data -- currently for one month only. When needed, the activity events are decrypted, parsed and filtered for the requested reports. The Windows Event Log provides a clean interception point for your customization needs: you can set event forwarding (into a SIEM system, for example), or otherwise copy the reporting data from that location.How to try this out?
In order to be one of the first in the world to try this out, you could download the Test Lab Guide from the connect site, install the connector on the Identity Manager server, and start viewing hybrid reports in Azure AD management portal. For instructions on how to download the latest Identity Manager beta, refer to my earlier post on this topic. As always, we appreciate any feedback or suggestion you may have! Thank you, Sharon Laivand
0
Likes
1 Comment
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.