- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity Blog
- Azure AD Connect & Connect Health is now GA!
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
First published on CloudBlogs on Jun 24, 2015 by the Microsoft Azure Active Directory Team
Howdy folks! I'm out this week coaching at the USA Volleyball Girls National Championships in New Orleans. But that doesn't mean the team slows down any. So today we're thrilled to announce the GA of Azure AD Connect and Connect Health! Samuel Devasahayam is the PM in the team who really has lead the charge here, so I've asked him to fill you in on the good news below. Best Regards, Alex Simons (Twitter: @Alex_A_Simons) Director of Program Management Microsoft Identity and Security Services Division Hi! For those of you who don't know me, I've been working in the Active Directory space since pre-Win2K days. My current job is to drive enhancements to Active Directory Federation Services (ADFS) and more importantly to enable a great connection experience to Azure AD. As Alex mentions we have been working hard to continue to provide a simple and great experience for hybrid organizations and we know you’ve been eagerly waiting for the GA release of Azure AD Connect . We’re thrilled to announce that as of today Azure AD Connect is now generally available for all Azure AD customers including Office365 customers. Azure AD Connect is the single tool and experience for connecting your on premises directories to Azure AD, whether you are evaluating, piloting, or in production. We are also pleased to announce that Azure AD Connect Health is also now generally available for our growing number of Azure AD Premium customers. Azure AD Connect Health is a cloud based service and a key part of our effort to help you monitor and secure your cloud and on-premises identity infrastructure. In this first release, Azure AD Connect Health provides customers who use ADFS with detailed monitoring, reporting and alerts for their ADFS servers. Read on more for additional details…
Azure AD Connect
Get Started Quickly and Easily Azure AD Connect lets you get started using your on premises identities with the cloud quickly and easily. Via a simple wizard based experience you can:
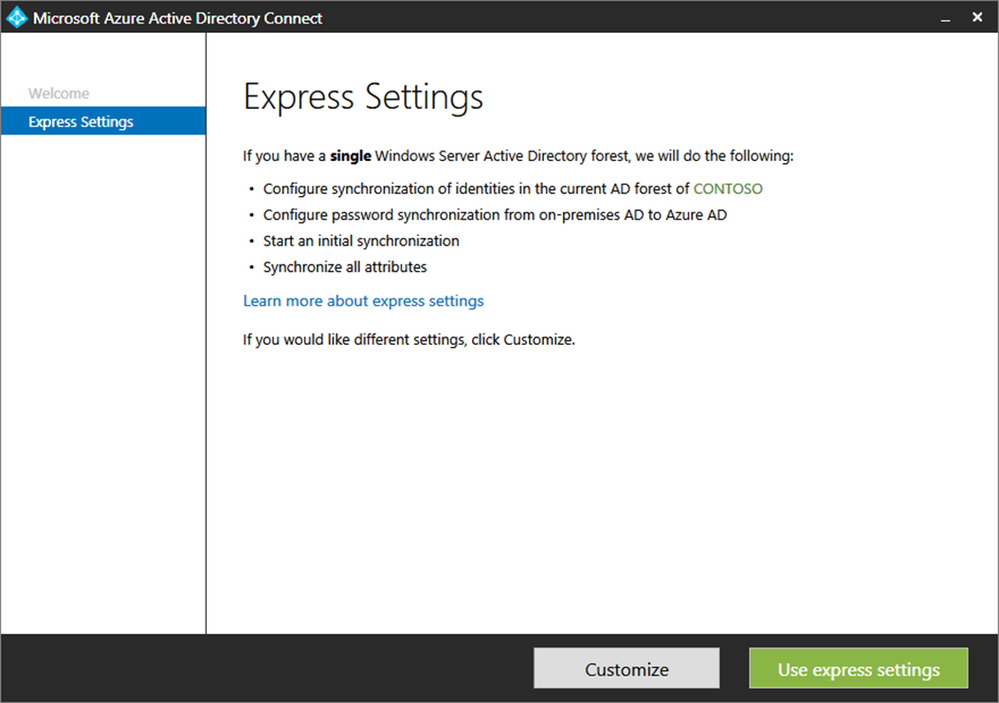
- Use Express Settings to connect a single AD forest to the cloud within minutes with just a few clicks!
- Pilot your connection to the cloud with a smaller set of users by specifying a group.
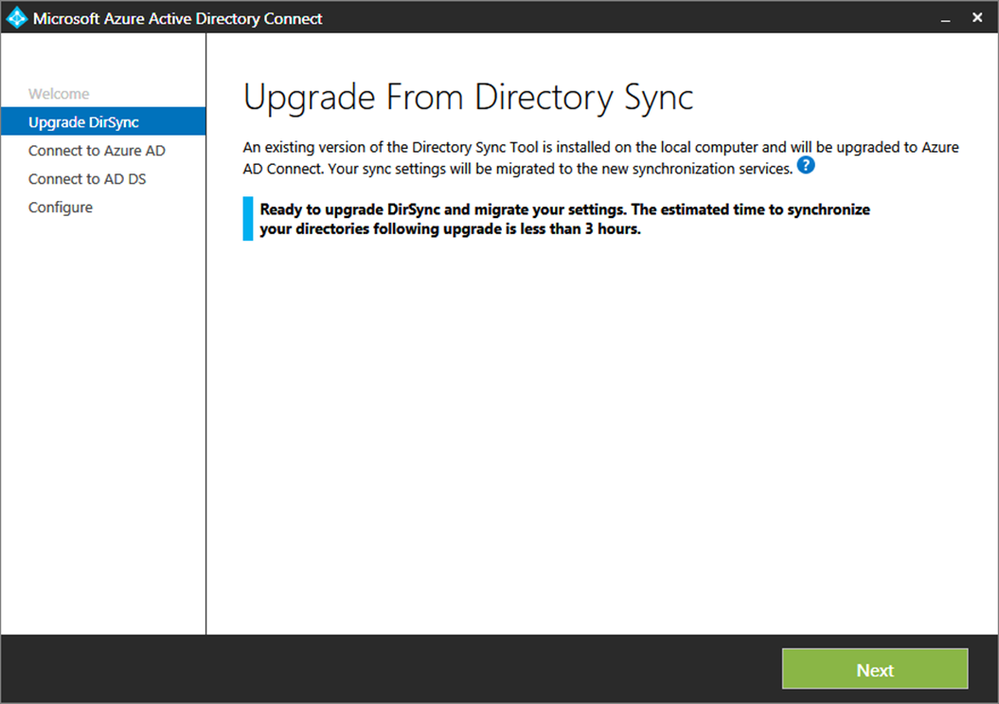
- Upgrade or migrate your existing Dirsync or AAD Sync deployment quickly and easily with little or no impact. Your existing sign-on solution through federation or password sync will continue to work as is
To start right away, download the release or check out our new Getting Started guide. You can also view a short video showing how easy it is to on board to Azure AD & Office 365. In the next few weeks we will also be updating the Azure AD portal to point to Azure AD Connect in place of Dirsync. If you’d like more details, please read on for more that you can do… Enable Rich Identity and Access Scenarios In addition to providing a simple experience, Azure AD Connect contains a rich feature set to enable identity and access management, self-service and conditional access control scenarios across cloud and on premises resources. With a rich set of sync and write-back capabilities, you can:
- Enable your users to perform self-service password reset in the cloud with write-back to on premises AD
- Enable provisioning from the cloud with user write back to on premises AD
- Enable write back of “Groups in Office 365” to on premises distribution groups in a forest with Exchange
- Enable device write back so that your on-premises access control policies enforced by ADFS can recognize devices that registered with Azure AD. This includes the recently announced support for Azure AD Join in Windows 10.
- Sync custom directory attributes to your Azure Active Directory tenant and consume it from your cloud applications
Support Common Enterprise and Organizational Needs Azure AD Connect custom options enable support for common organizational needs and topologies as well:
- Connect multiple AD forests at one time to integrate users, groups and contacts that may live in one or more forests
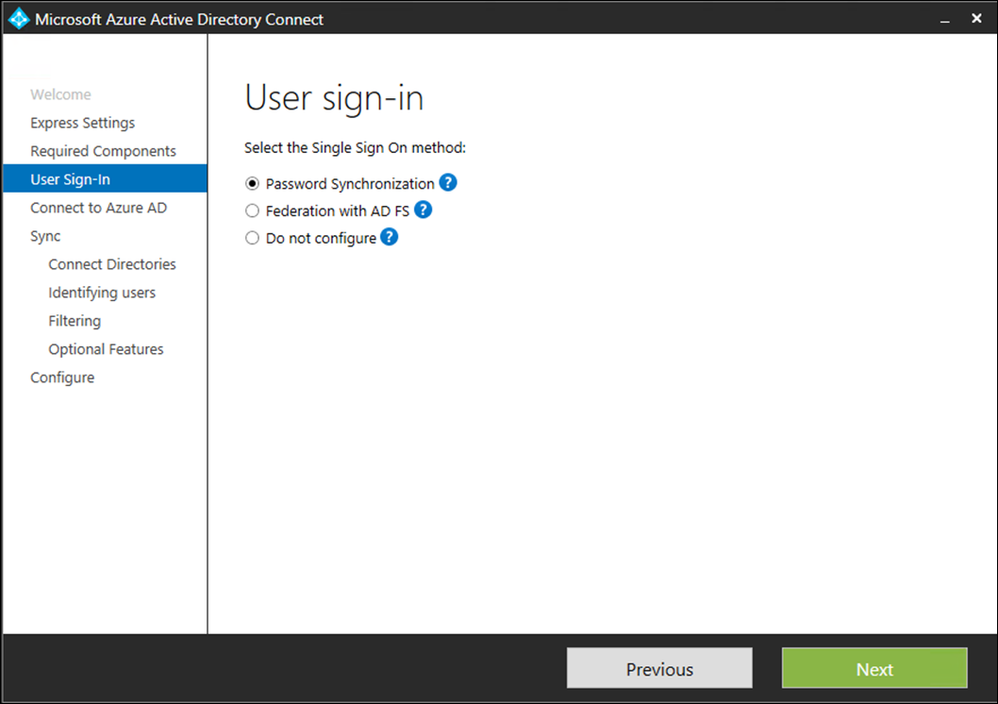
- Configure password sync or federation for your sign-in needs. Choosing federation provides you with a simplified and streamlined deployment of ADFS
- Stage your sync cutover process or setup a new “hot spare” using “staging mode” for sync
- In addition, the latest version of the sync engine allows you to reduce risk with a new delegated Azure AD role and account for sync, and prevent accidental deletions with new sync deletion thresholds.
Additional options Once you setup your initial connection, it is easy to use Azure AD Connect to scale or add additional options:
- Add additional on-premises Active Directory forests
- Add additional Azure AD domains or scale up your connection for federated SSO
Azure AD Connect Health
Every day, over 25,000 customers use Active Directory Federation Services (ADFS) to enable seamless sign-in to Office 365 and other Azure AD applications. As you can see from our blog post earlier this year, 32% of all Azure AD logins use ADFS to enable user sign-in. Using ADFS for user sign-in to Azure AD does require you to run the service in a reliable and highly available manner, and as such it is important that you have the right tools to monitor service quality. We are pleased to announce the general availability of Azure AD Connect Health, a feature of Azure AD premium , to monitor your ADFS servers. This feature makes it easier for IT organizations run their ADFS systems reliably and gain insight into health, performance and login activity. While this first release supports monitoring ADFS, we are actively working on enabling monitoring for other identity infrastructure components such as the sync service in Azure AD Connect in the near future. This release for ADFS has 3 key capabilities:
- Alerts based on events, configuration information, synthetic transactions and perf data. So, when something goes wrong, or is about to go wrong, we let you know.
- Graphs of login activity that you can pivot multiple ways for easy viewing. These "usage insights," are accessible when you enable auditing on your ADFS servers. They are based on audits generated when user's login and tokens are generated for applications.
- Access to key performance indicators across multiple servers, including token request counters, processor, memory, latency, and so forth
You can read more about this in our Getting Started guide and from our blog post earlier this year. There are a few key enhancements we’ve made since our preview. Read on more for additional details on these. Email Notification for Critical Alerts Getting notified when something goes wrong is important for IT administrators so that they can proactively look for issues. This is something that we've heard consistently from our preview customers. We’ve made it super easy for you to add specific people or distribution lists to send notifications for any critical alert that is detected. 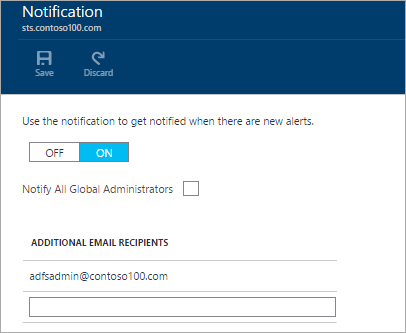

What’s next?
We are already working on our next release to provide additional scenarios to Azure AD Connect and Azure AD Connect Health. These include
- Deployment integration of Azure AD Connect Health & Azure AD Application proxy
- Additional sync and sign on options
- Azure AD Connect Health for Sync
We’re looking forward to your feedback at our discussion forum or feel free to add comments to this post. Thanks, Sam (@MrADFS) with the awesome support of the Azure AD Connect & Connect Health teams.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.