- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity Blog
- Azure AD Connect Health for sync is now in Public Preview!
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
First published on CloudBlogs on Nov 05, 2015 by the Microsoft Azure Active Directory Team
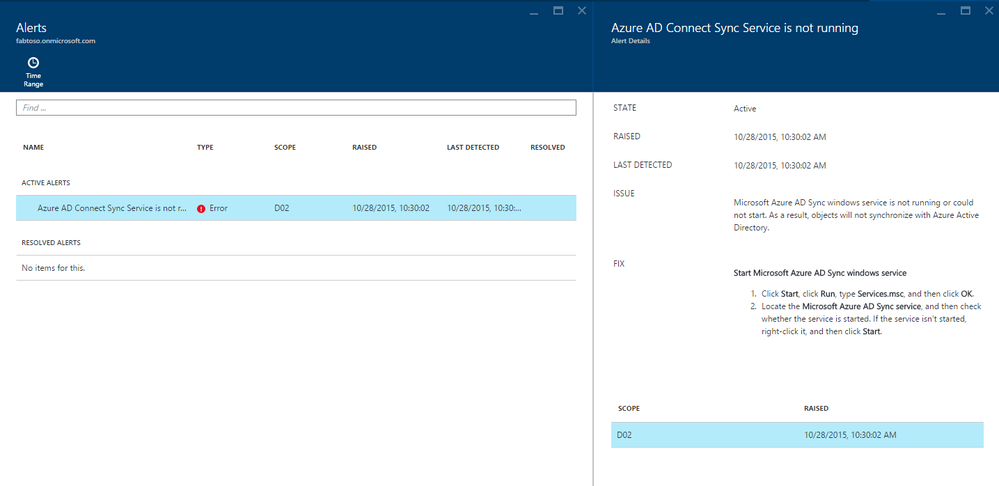
Howdy folks! I’m Sam and I lead the PM team on our Azure AD Connect efforts within the Identity team here at Microsoft. We released Azure AD Connect , the one-stop deployment experience to integrate your on-premises directory with Azure AD early in summer this year. In a majority of the cases, customers are up and running in a matter of minutes. We continue to make updates on an on-going basis with new features. So, get to the latest version of Azure AD Connect (downloadable via this link ) if you have not done so already. Most of you have heard of great end user facing functionality of Azure AD Premium that makes the lives of your information workers simple and enables better productivity with great features such as self-service password change/reset , SSO to thousands of SaaS applications or Azure AD Application Proxy for extranet access. Azure AD Premium also provides great admin facing functionality that enables you to manage your identity infrastructure efficiently and at lower cost. Azure AD Connect Health is one such feature that provides monitoring and insights capability for your on-premises identity infrastructure. We released monitoring and insights for AD FS servers so that you can manage a reliable infrastructure critical to connecting up to Azure AD applications such as Office 365. I’m really excited to announce the expanding portfolio of Azure AD Connect Health with the public preview of Connect Health for sync that allows you to monitor and gain insights into the sync service of Azure AD Connect. As an admin you are now armed with the tool set to ensure that your end users have reliable access to their productivity & business applications. The service provides alerts and email notification for the sync service. For example, if your sync service is down, you will be alerted in the portal and receive notification to the email addresses that you have configured. You can learn more about how the alert mechanism works in this detailed blog post .
How do I install this?
We’ve made installation simple & seamless as part of your Azure AD Connect servers. All you have to do is
- Install the latest version of Azure AD Connect on Microsoft Download Center . For existing customers of Azure AD Connect, this is a seamless upgrade.
- Access the Azure AD Connect Health portal here . Do ensure that you have an Azure AD premium subscription and have a license assigned to you prior to accessing the portal.
That’s it! Your all set up. No fuss, no frills :) and have access to what your sync service is doing from anywhere in the world! 
What’s coming next?
We are actively working to add the following capabilities that will be available in the near future. These are:
- Additional alerts to detect more error conditions from our experience with customers.
- Insights into the trend of changes that are being exported to Azure AD. You will be able to use this to analyze any spikes while troubleshooting.
- Insights into the latency of sync operations that can help you fine tune your sync servers
All these features will require no additional deployment for you and highlights the power of cloud services to provide additional value on an on-going basis.
Additional features released for Azure AD Connect Health
As a cloud service, we continue to update the service with additional capabilities and provide value to you. We’ve added a few additional capabilities in Connect Health since our GA in early summer this year. These are:
- RBAC support to delegate access to Azure AD Connect Health . This feature allows Azure AD global admins to delegate access to Connect Health to other users without the need to making them a global admin. No more needing to be an Azure AD global administrator for actions that don't require this highest level of access. You can read more about this feature here .
- Top users with failed username password logins for ADFS . This feature allows your admins to investigate the users with a high # of bad passwords and determine if this is a security issue or caused by an app that is using expired passwords. You can read more about this feature here .
Note: If you don’t have Azure AD premium, getting a trial is easy. Follow the instructions available for a free 30-day trial via this link . As always, if you have any feedback or additional capabilities that you would like to see, leave a comment in this post or tweet me (@MrADFS). Your feedback is valuable to us. Thanks //Sam (@MrADFS)
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.