Microsoft recognized as a Leader in the Forrester Wave™: Workforce Identity Platform, Q1 2024
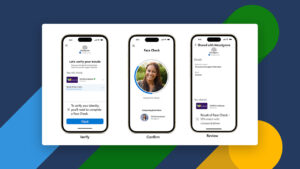
We’re thrilled to announce that Forrester has recognized Microsoft as a Leader in the Forrester Wave™: Workforce Identity Platforms, Q1 2024 report. We’re proud of this recognition, which we believe reflects our commitment to delivering advanced solutions that cater to the evolving needs of our customers in the workforce identity space.