
Solve IT governance and admin challenges with new features for Power Platform
To respond to the growing demand for digital solutions, organizations are increasingly looking for ways to drive accelerated app innovation. Low-code platforms like Microsoft Power Platform help IT professionals move faster through collaboration with the business allowing for delivery of more solutions with greater efficiency, security, and compliance.
Current market conditions are challenging for IT professionals to manage security and deliver customer expectations timely, given that “remote everything” is the new reality. According to Gartner*, “The advent of cloud computing and the movement to more rapid, DevOps-style application development strategies has placed significant stresses on IT operations teams. Pair this with internal democratization of information and technology (I&T) and movements toward citizen-developer ‘low code’ application and automation platforms, and the role and importance of IT operations teams has never been more prominent leading into 2021.”
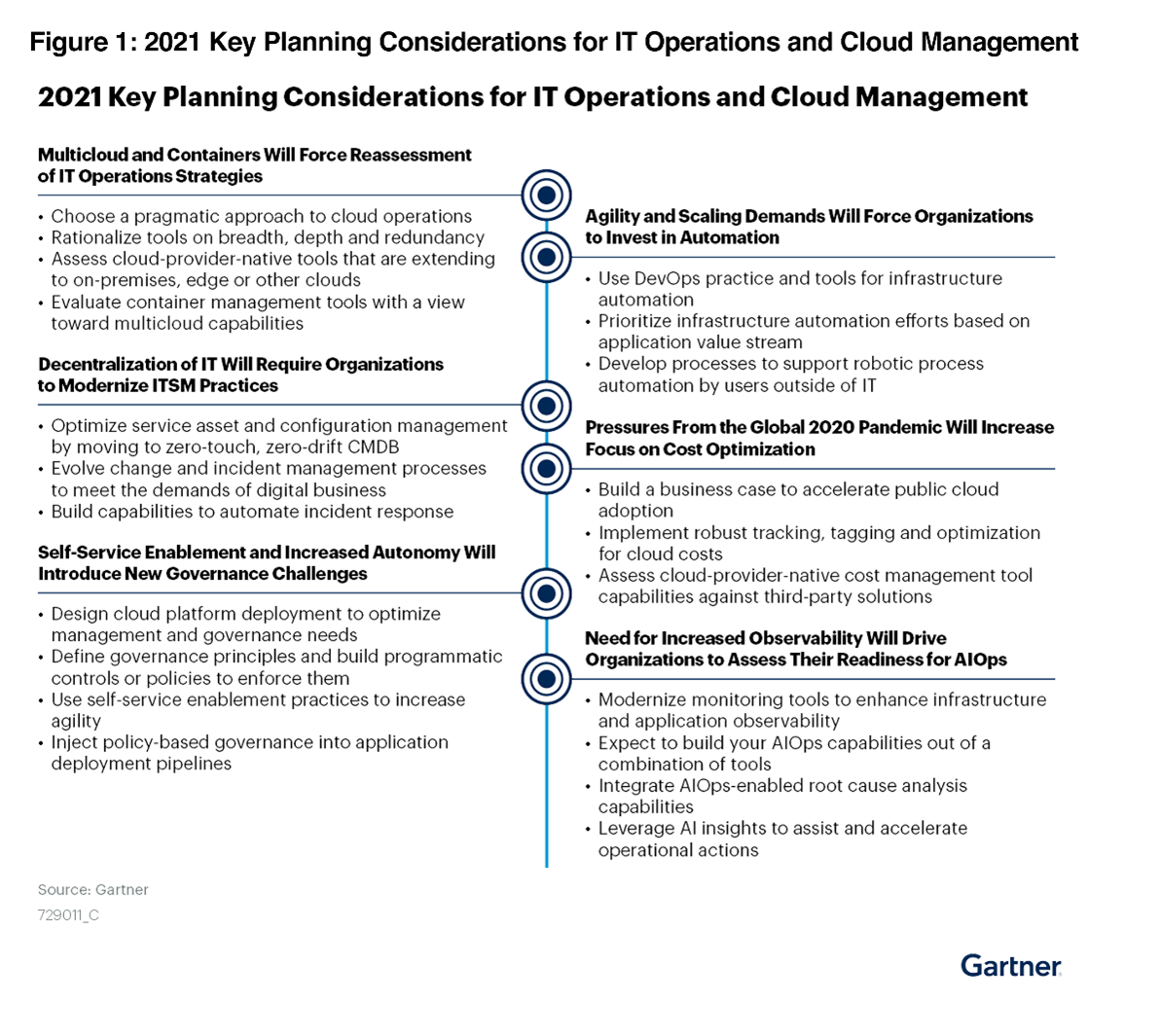
*Gartner, 2021 Planning Guide for IT Operations and Cloud Management, 9 October 2020, Douglas Toombs, Lydia Leong, Alan Waite, Marco Meinardi, Tony Iams, Steve White, Venkat Rayapudi, Brian Adler, Paul Delory, Gregg Siegfried, Gregory Murray, Simon Richard, Elias Khnaser.
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available by accessing with your Gartner account.
How do you scale traditional IT governance and administration to meet this growing demand? Microsoft Power Platform provides an ideal platform for creating rich customer experiences with managed services built for IT professionals, admins, and operators alike. Power Platform takes the platform one step further, enabling you to leverage the efficiency of low code without compromising security and administration standards.
Solving key customer IT governance and administration challenges across Power Platform
Easier IT governance and administration can help customers accelerate the development and management of applications that historically take longer to release and cost more money.
As adoption of Power Platform continues to grow to meet demand, the concept of Enterprise Trust becomes important in ensuring Chief Information Security Officers and IT departments are comfortable and encourage citizen development growth in their organizations. Building on the Power Platform professional developer momentum from Microsoft Ignite in 2020, we have made significant improvements over the past six months to ensure IT professionals have an accelerated path to securing and monitoring Power Platform, allowing their citizen and professional development to succeed.
Admin visibility and oversight across all aspects of Power Platform
A key aspect for admins to securely deploy and effectively support a low-code or no-code platform is the ability to monitor usage and business impact across the entire tenant. Power Platform monitoring tools make it easy for enterprises to get full visibility of what their employees are building and how these apps and flows are getting used. This is a key difference from other IT development projects, where IT teams traditionally struggle to gain a full understanding of usage and data access. We have recently introduced many new monitoring and manageability features simplifying our customer’s IT governance journey, and we will continue to add deeper insights and new features in this space. Stay tuned!
Out of the box tenant-wide analytics
Using the Power Platform admin center, administrators have been able to use the built-in reports for apps and flows available for every environment to track usage and maker activity. We are announcing new tenant wide reports for apps and flows that enable admins to track overall usage and business impact of the platform across all environments, identify top maker trends, and review sharing details for key Power Platform resources.
Extensive filtering support allows admins to dig deeper into the analytics and slice and dice the data. With available inventory list views of apps and flows these reports can be easily downloaded by admins as a CSV file for deeper analysis.
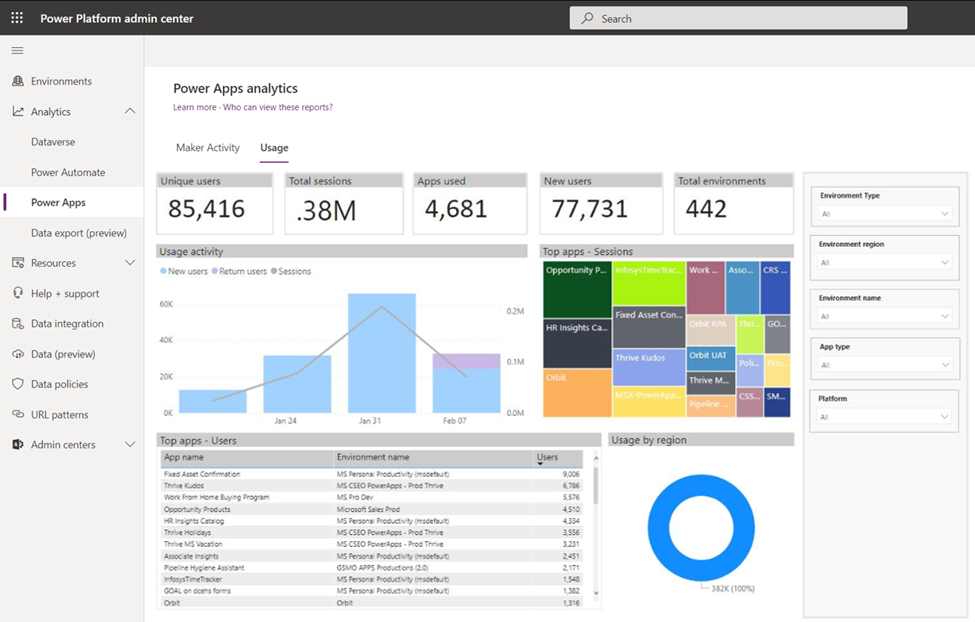
Usage reporting: Power Apps and Power Automate
We are introducing tenant-wide reporting in Power Platform admin center, which provides insights into the trends of active users and overall sessions, so you can quickly see how many users across your organization are using Power Platform apps and flows across all your environments in a single view.
The Microsoft Power Apps usage reports allow you to gain visibility into monthly active user trends as well as identify net new users. The top applications, calculated by their usage are listed in an inventory view, allows admin teams to further identify relevant details about the most impactful Power Platform assets in their organization such as Environment name, Unique users, Total sessions, or Last launch time of each individual app or flow.
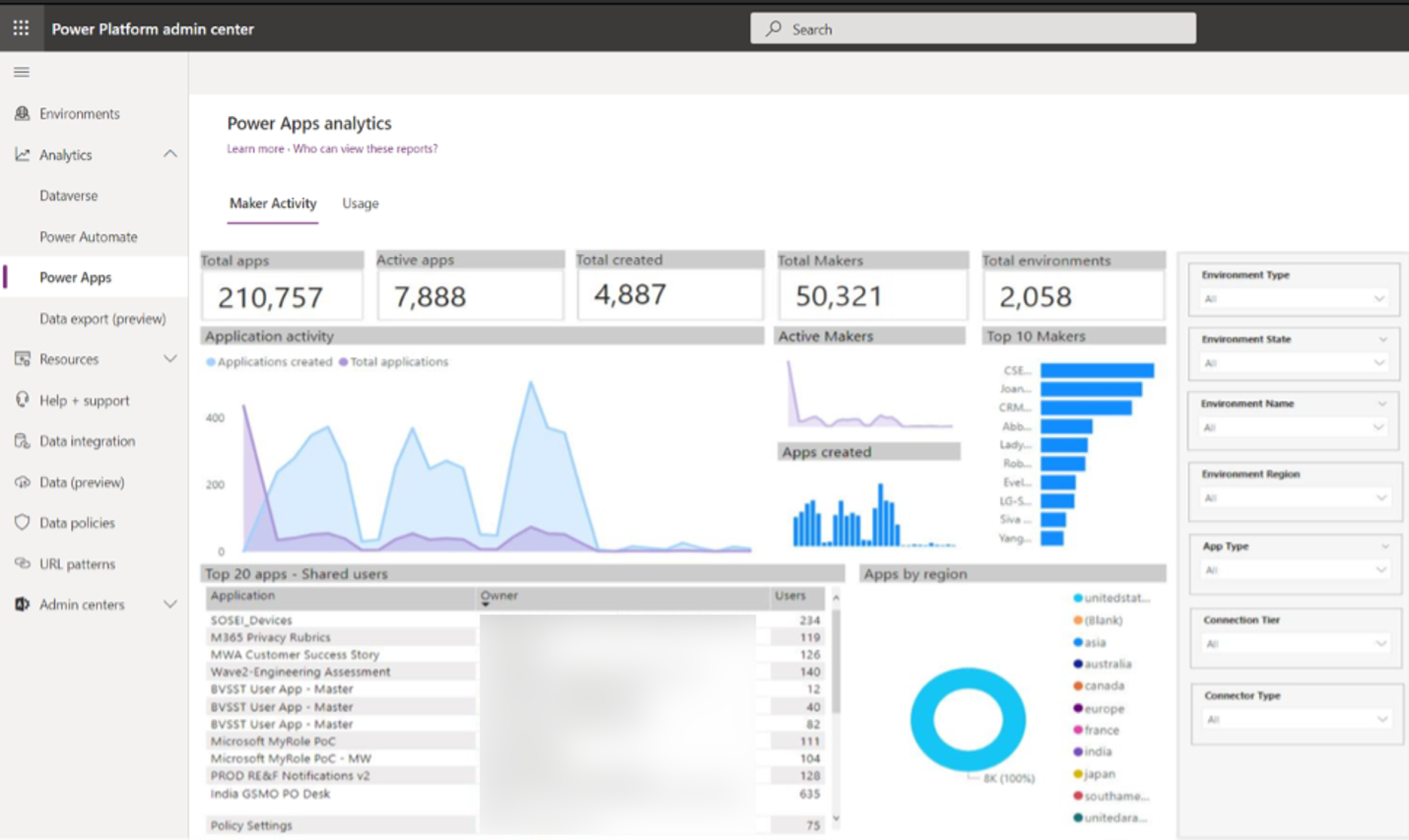
Maker activity reporting: Power Apps and Power Automate
This report shows you the trends of app and flow creation as well as overall maker ecosystem trends across your tenant.
The Power Apps Maker Activity reports allow you to analyze monthly app creation and maker trends in the organization. The most recently created are listed in an inventory table view allowing admin teams to further identify relevant details Power Platform assets in their organization such as Maker or Owner name, Environment name, sharing details, State, or Created time of each individual app or flow.
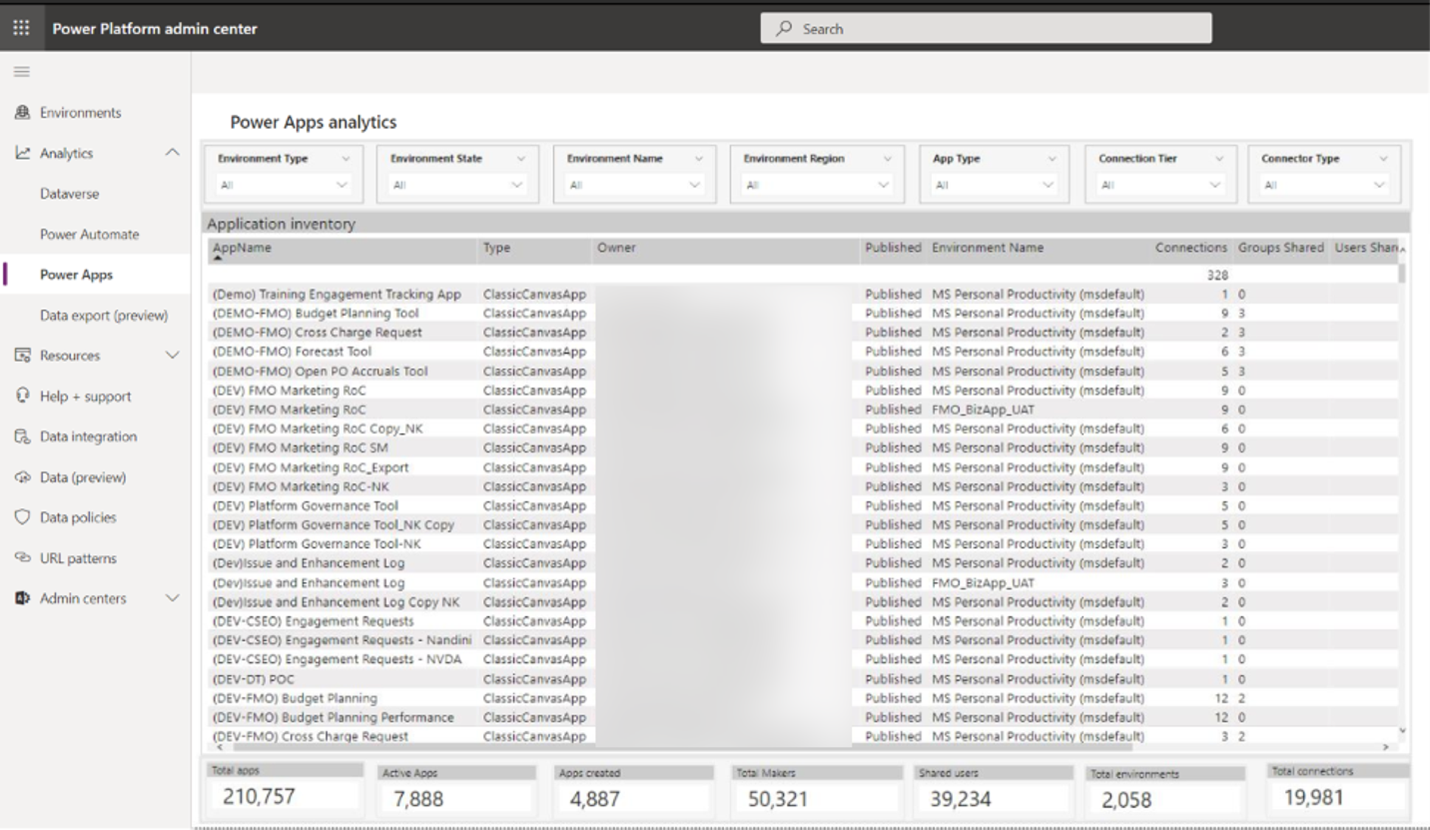
Inventory reporting: Power Apps and Power Automate
Apart from usage and maker activity reporting, admins will also be able to visualize the full tenant app and flow inventory in a list view with relevant details along with extensive filtering support to identify the resources that are adding the most (or least) value to their enterprise. All inventory list views can be exported by admins leveraging the embedded Microsoft Power BI capability.
Proactive controls to secure and govern your enterprise data within Power Platform
As low-code and no-code platforms usher in the digital revolution in the enterprise, security architects and admins want the ability to ensure that their data is safe. Power Platform is built on Microsoft security standards including the strong security and compliance features of Microsoft Azure and Microsoft Azure Active Directory (Azure AD). We have released many targeted security and governance capabilities that enable environment- and tenant-wide data exfiltration governance, fine-grained data loss prevention rules for connector actions and endpoints, as well as Data Loss Prevention support for custom connectors.
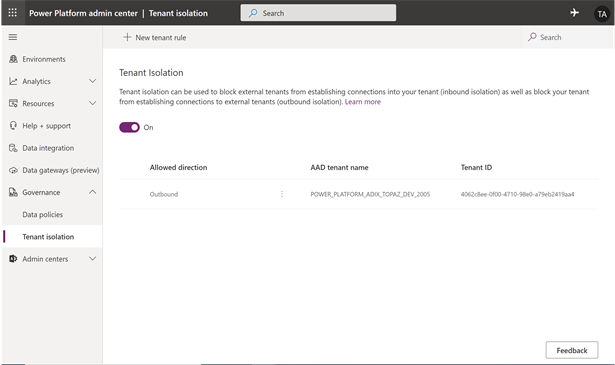
Tenant isolation
An organization’s data is its most important asset, and Power Platform admins can now securely enable environments to embrace citizen developers by offering strong data exfiltration controls. We have recently enhanced the cross-tenant inbound and outbound restrictions for Power Platform connectors leveraging Azure AD based authentication such as Office 365 Outlook or SharePoint. Organizations can now opt to isolate the tenant for Azure AD-based connectors exclusively for Power Platform, using the tenant isolation capability in Power Platform admin center.
Admins can configure tenant isolation for Power Platform, ensuring that any inbound connections to the tenant from external tenants, as well as outbound connections from the tenant to external tenants are blocked for all AAD-based connectors. Based on business requirements, tenant admins can also choose to allow one or more inbound and outbound connections in specific tenants while disallowing all other tenants.
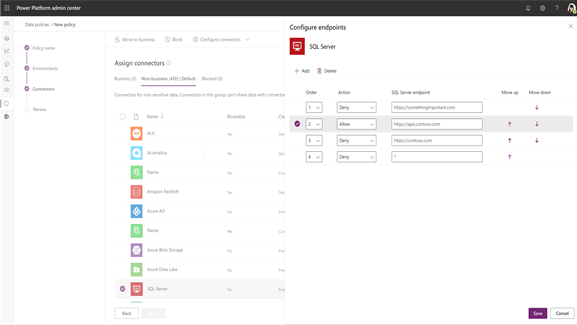
Endpoint filtering for connectors
Data Loss Prevention control allows admins to configure specific endpoints to allow or block for important connectors such as SQL, Microsoft Dataverse, HTTP, SMTP, and Blob storage. More connectors will be added to endpoint filtering soon.
Admins can add endpoint names as an ordered list of endpoint entries that will be evaluated from Rule 1 to N. Asterisk-based pattern matching is supporting for the list entries, making the configuration easy for admins. During Data Loss Prevention policy enforcement, apps and flows honor “allow or deny” actions specified against the first matched endpoint entry in the list.
This capability empowers admins to facilitate the use of important connectors for business use cases in relevant environments with specific endpoints only. The ability to block risky endpoints from being reachable through Power Platform connectors enables admins to safely empower their business users without incurring the risk profile of the underlying service potentially exposing sensitive data sources within their organization. For example, an admin may choose to allow only specific instances of SQL servers to be reachable in an environment while blocking others through the SQL connector. This configuration will allow business users to create apps and flows leveraging specific SQL servers as a data source while ensuring that any sensitive information across finance or HR SQL servers cannot be accidentally exposed by the makers.
This feature will also allow admins to insert a “Deny *” or “Allow *” rule at the end of the list as the default setting for new endpoints reachable through the connector to be allowed or blocked by default until admins get a chance to review and appropriately classify them.
Fine-grained controls in Data Loss Prevention policies
Power Platform offers access to more than 400 connectors to today’s most popular enterprise applications. Connectors are proxies or wrappers around an API that allows the underlying service to connect to Power Platform. Controlling access to these connectors and the data residing in the applications is a crucial aspect of a proactive governance and security approach. Data loss prevention offers effective grouping of connectors across business, non-business, and blocked categories. Recently we have also introduced fine-grained Data Loss Prevention controls such as Connector Action Control and Endpoint Filtering that will allow admins to balance business productivity and data security.
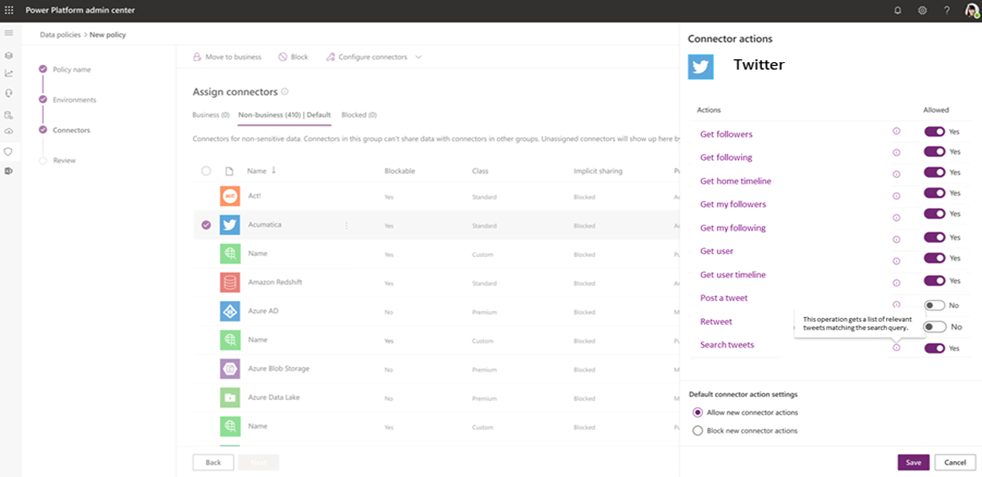
Connector Action Control
As the name suggests, the new connector action control capability allows admins to enable important connectors for business use cases in relevant environments with specific actions only. Using connector action control, admins can decide which specific actions will be allowed or blocked for a given connector. The ability to turn off risky connector actions enables admins to safely empower their business users without incurring access risk to the underlying service. For example, an admin may choose to allow only read actions for the Twitter connector in an environment, while disabling write actions such as posting a tweet and retweeting. This configuration allows marketing departments to create apps and flows to conduct sentiment analysis using the Twitter connector while giving admins the peace of mind that Power Platform cannot be used to post tweets.
This feature also allows admins to choose a default setting for new actions being added to an existing connector and classify them as allowed or blocked by default until admins get a chance to review and appropriately classify them. Connector action control will not be supported for unblockable connectors such as standard licensed Office 365 connectors.
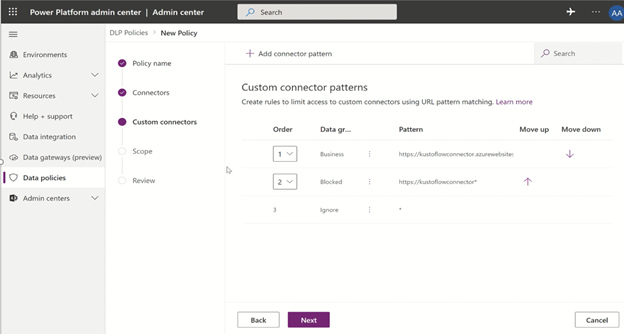
Custom connector governance: URL filtering within data loss prevention policies
Another new capability is the support for custom connector governance through tenant-level Data Loss Prevention policies. Until recently, custom connectors could only be added to environment level Data Loss Prevention policies through PowerShell. UI support and tenant-level policy support for custom connectors was not available.
While custom connectors themselves are environment-scoped resources, admin security and governance policies should apply to URL endpoints as a singular risk profile versus every single custom connector created with the same underlying URL across different environments.
The new Data Loss Prevention custom connector capability now allows admins to:
- Specify an ordered list of host URL patterns (including asterisk-based support) for custom connectors in tenant-level policies and classify them as “business,” “non-business,” or “blocked” through Data Policies in the Power Platform admin center as well as PowerShell. Additionally, the last rule of the custom connector URL pattern list can be set up to “ignore *’ ensuring that admins can defer management of custom connectors through environment level policies if desired.
- Set up custom connector classification (by name of the connector) from Data Policies in the Power Platform admin center for environment level policies as well as PowerShell.
Email exfiltration controls
In addition to leveraging the Power Platform tenant isolation capability to prevent data exfiltration and infiltration for Azure AD-based connectors by disallowing connection establishment, admins can now also use the Power Platform email exfiltration control for Office 365 mail connectors to ensure that no emails can be distributed outside the organization without admin approval or oversight.
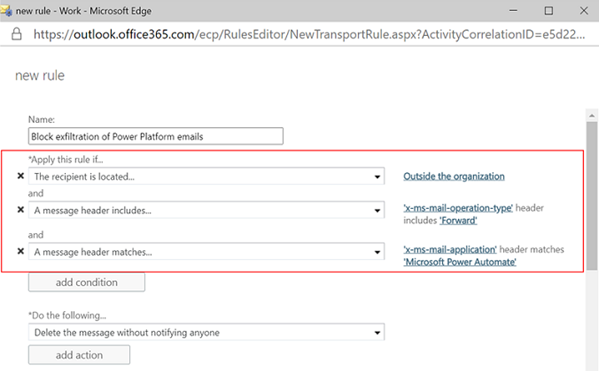
With complete coverage on risks of data exfiltration for any shared environments, such as default environment, through email exfiltration for external mail recipients, tenant isolation for controlling Azure AD-based connectors, admins can now safeguard against connectors using external identity providers (non-Azure AD) by creating a data loss prevention policy which classifies these connectors under the “blocked” group while selectively enabling these for specific makers in their production and sandbox environments based on business requirements.
As the need for custom applications increases faster, IT professionals, administrators, and operators can feel confident that Power Platform has been built from the ground up to ensure you achieve your goals now and into the future.
Power Platform customers benefiting from rich governance and administration
“By connecting our Power Platform developers directly with business owners, we’re able to identify opportunities faster and solve business problems at scale.”—Alan Chai, Head of Digital Transformation & Innovation, Schlumberger
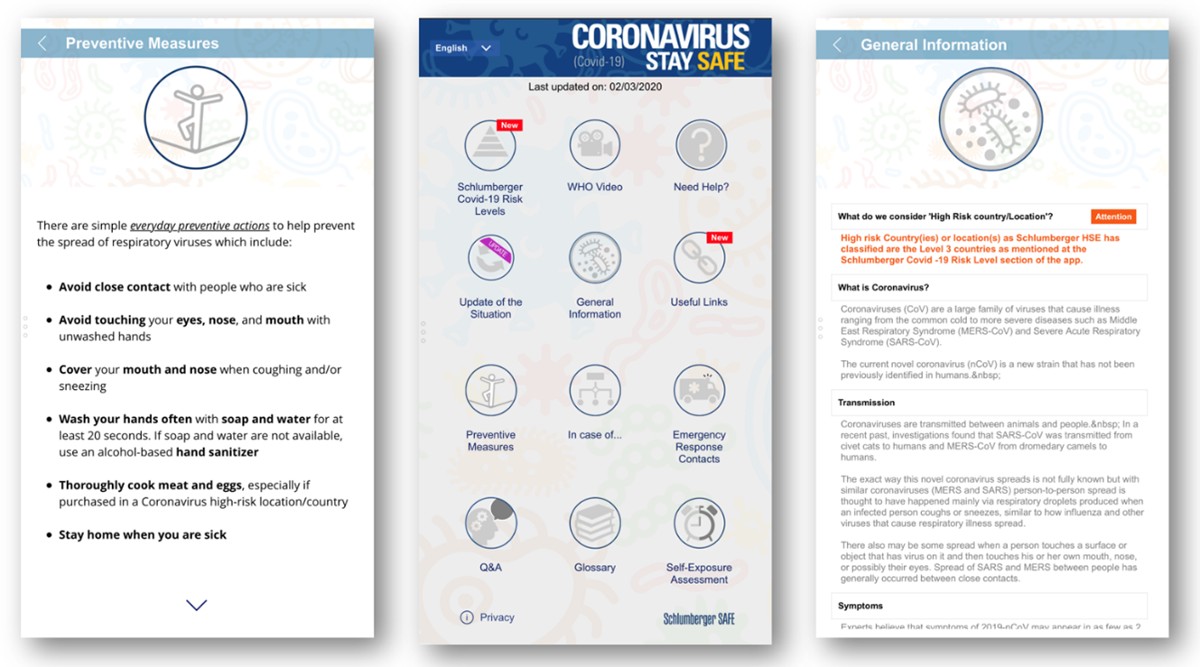
Learn more about how Schlumberger is solving business problems faster and at scale with Power Platform.
![]()
“The main reason we have citizen development is to battle against shadow IT. It’s all about visibility.”—Chris Ingalls, Portfolio Architect, Toyota North America

Learn more about how Toyota improves efficiency and speeds innovation with Power Apps.

“Microsoft Power Platform has allowed us to break free of the challenges we had with custom code and innovate quickly on top of our legacy systems.”—Bob Means, Director of Business Solutions, Coca-Cola Bottling Company United

Learn more about how Coca-Cola UNITED manages rapid growth with Power Platform.
“We’ve been excited to see how the Power Platform can automate manual processes, help us to manage COVID-19, but it’s not just about building the apps. The new Power Platform governance features enable us to build them with a strong foundation of governance, security and stability.”—Julie Mercer, Collaboration Services Director, Unilever
Resources to help you get started with Power Platform governance and administration
- Webinar: Introduction to governance capabilities
- Webinar: Surround SAP with Power Platform for quick value and time to market
- Webinar: Unified IT management experience
- Session: How to responsibly scale Power Apps in your organization with a Low Code Center of Excellence
- Blog: Why low-code will be big in your 2021 tech strategy
- Blog: Recent enhancements for Power Platform governance
- Web: Learn how IT Professionals can benefit from using Power Platform
- Whitepaper: Power Platform administration and governance
- Gartner report: the composable enterprise for IT Leaders
- Docs: Power Platform guidance documentation



