Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Home
- Microsoft Intune and Configuration Manager
- Configuration Manager Archive
- Configuring IKEv2 profiles for Windows Phone devices using Configuration Manager and Microsoft Intune
Configuring IKEv2 profiles for Windows Phone devices using Configuration Manager and Microsoft Intune
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Published
Oct 16 2018 06:40 PM
695
Views
Oct 16 2018
06:40 PM
Oct 16 2018
06:40 PM
First published on CLOUDBLOGS on Dec 03, 2014
Author: James Lieurance, Software Engineer, Enterprise Client and Mobility
Many organizations are beginning to evaluate and provision Windows Phone 8.1 to their employees, largely due the many improvements to platform manageability. Microsoft Intune and System Center 2012 R2 Configuration Manager provide extensive support for managing Windows Phone 8.1, and one commonly utilized feature is the ability to configure VPN profiles so that devices can seamlessly connect to secure corporate resources. This blog article outlines the process for setting up an IKEv2 VPN profile and deploying it to Windows Phone devices.
Because Configuration Manager and Intune support multiple VPN profile types across various platforms, it is important to understand which input parameters and values are normally required for Windows Phone 8.1. This blog details three commonly configured profiles.
Wizard page 1: Create a new VPN profile, providing a name that will be used to identify it in the Admin Console.

Notes:
This name is used in the Admin Console and on the Window Phone device. You can also provide an optional description. Keep in mind that the display on a phone might not be able to display all of a long name.
Importing an existing VPN profile is not supported for Windows Phone devices.
Wizard page 2: Configure the Connection Type (IKEv2), default server, Full-tunneling, DNS Suffix, and Bypass on corporate Wi-Fi .

Notes:
You need at least one (default) server for a VPN connection.
“Send all network traffic through the VPN connection” is the checkbox that determines Full vs. Split tunneling. If unchecked, you should provide Destination Prefix Metrics (e.g. Routes) which are shown in the Split tunneling example below.
Connection specific DNS suffix is the DNS that will be used once the connection is started.
“Bypass VPN when connected on company Wi-Fi network” checked means the VPN connection will not be automatically started when device is already on a corporate Wi-Fi connection. A user can still start the VPN connection manually.
Wizard page 3: Configure Authentication method properties and Remember Credentials checkbox

Notes:
EAP-MSCHAPv2 is a commonly used secured password authentication method.
Most EAP-based authentication methods require extra configuration provided through the “Configure” button.
For EAP-MSCHAPv2, the configuration is fairly simple. “Automatically use my Windows logon name and password” will use the currently logged on user. For a Windows Phone device, this might be the end-user’s private account that the phone was set up with (BYOD). The end-user would then enroll using their workplace credentials which would not be considered the logged in user. We suggest leaving that box unchecked so the end-user can provide their workplace credentials when prompted on their BYOD Windows Phone 8.1 device.
You can check “Remember the user credentials at each logon” so that the end-user will have their credentials saved once they have provided them for the initial VPN connection.
Wizard page 4: Configure proxy settings

Notes:
Proxy settings are optional. If your VPN connection / environment requires a proxy for the VPN connection then this is where you would configure it for your Window Phone 8.1 VPN profile.
Wizard page 4: Configure the DNS Suffix Search List

Notes:
Intune only supports the DNS Suffix search list setting for VPN profiles deployed to Windows Phone 8.1 devices. Each entry is a specific DNS suffix that will be searched when connecting to a website using a short name. For example: “http://MyWebSite” would be searched for as MyWebSite.contoso.com, MyWebSite.childdomain1.contoso.com, etc…)
Wizard page 5: Configure applicable platforms

Notes:
VPN profile deployment is supported on Windows Phone 8.1 and newer devices.
Configure routes to enable Split-tunneling:
Notes:
“Send all network traffic…” box checked – enables force tunneling; unchecked - enables Split-tunneling
Routes will need to be set to tell the device when to use the VPN connection. If the network traffic has a destination that matches a Route/Destination Prefix, then the device will split that traffic onto the VPN connection. Any other traffic that does not match a route will not use the VPN connection.
All other wizard pages would be configured the same as above.
Configure EAP-TLS (cert-based) authentication

Notes:
“Smart Card or other certificate” is the EAP-TLS authentication method.
For the device to be able to find and use the correct certificate for the connection you need to configure EAP-TLS properties for your environment including the “Advanced” page.
Verifying the server’s identity is not required but is recommended.
Having the EKU set correctly with Client Authentication added under the “AnyPurpose” section is required.
All other wizard pages from above would be configured the same.
Deployment Wizard: Deploy to User or Device collection
Notes:
We support deploying VPN profiles to User or Device collections.
You can configure an alert to be generated if compliance does not meet the SLA (Optional)
Schedule: This pertains to only the Windows on-premises client evaluation schedule. Windows Phone devices sync with the server and evaluate policies on their own schedule (default of every 8 hours).
Monitoring deployment of the VPN profile.
Compliant results look like this:

Error example:

Notes:
In this instance various settings failed to remediate. If these types of errors are seen then the suggested step would be to check the device for the profile. If only one setting reported failure that could just be due to a setting or value that is not supported by the Windows 8.1 device and the profile may have been placed on the device anyway. If you see various remediation errors like the example above then most likely the profile was not able to be placed on the device because of some issue with the device itself.
Checking the Window Phone 8.1 device for the profile:
You can find the VPN profiles under Settings -> VPN
Notes:
The active profile is the one that will be connected or triggered. Tap a different profile to activate it. Tap and hold on a specific VPN profile to view details or edit its properties:

This document provides some examples of working IKEv2 VPN profile configuration. Of course every environment will be different and changes to the examples above would be needed but hopefully this information will guide you in the right direction.
Whenever in doubt, try creating the profile on the device manually to confirm that you understand how the profile should look in order to connect to your VPN server. If you cannot get your device to connect with a manually created profile then deploying a similar profile through the Configuration Manager console will likely not work either.
For more information about using VPN profiles in Configuration Manager, see VPN Profiles in Configuration Manager in the Configuration Manager Documentation Library .
--James Lieurance
Configuration Manager Resources
Documentation Library for System Center 2012 Configuration Manager
Configuration Manager 2012 Forums
System Center 2012 Configuration Manager Survival Guide
System Center Configuration Manager Support
This posting is provided "AS IS" with no warranties and confers no rights.
Author: James Lieurance, Software Engineer, Enterprise Client and Mobility
Many organizations are beginning to evaluate and provision Windows Phone 8.1 to their employees, largely due the many improvements to platform manageability. Microsoft Intune and System Center 2012 R2 Configuration Manager provide extensive support for managing Windows Phone 8.1, and one commonly utilized feature is the ability to configure VPN profiles so that devices can seamlessly connect to secure corporate resources. This blog article outlines the process for setting up an IKEv2 VPN profile and deploying it to Windows Phone devices.
Creating a VPN Profile for Windows Phone 8.1
Because Configuration Manager and Intune support multiple VPN profile types across various platforms, it is important to understand which input parameters and values are normally required for Windows Phone 8.1. This blog details three commonly configured profiles.
IKEv2 VPN using password-based authentication and full-tunneling
Wizard page 1: Create a new VPN profile, providing a name that will be used to identify it in the Admin Console.

Notes:
This name is used in the Admin Console and on the Window Phone device. You can also provide an optional description. Keep in mind that the display on a phone might not be able to display all of a long name.
Importing an existing VPN profile is not supported for Windows Phone devices.
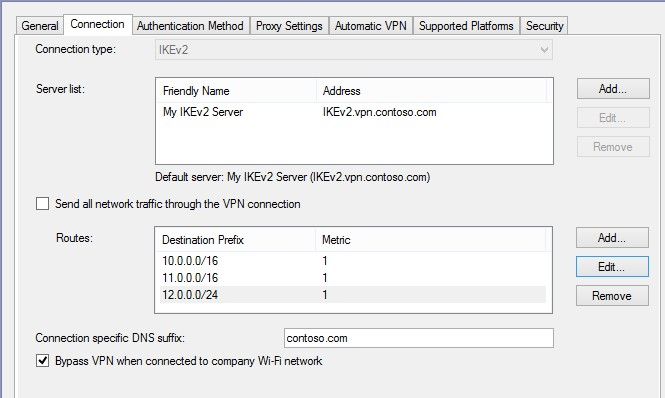
Wizard page 2: Configure the Connection Type (IKEv2), default server, Full-tunneling, DNS Suffix, and Bypass on corporate Wi-Fi .

Notes:
You need at least one (default) server for a VPN connection.
“Send all network traffic through the VPN connection” is the checkbox that determines Full vs. Split tunneling. If unchecked, you should provide Destination Prefix Metrics (e.g. Routes) which are shown in the Split tunneling example below.
Connection specific DNS suffix is the DNS that will be used once the connection is started.
“Bypass VPN when connected on company Wi-Fi network” checked means the VPN connection will not be automatically started when device is already on a corporate Wi-Fi connection. A user can still start the VPN connection manually.
Wizard page 3: Configure Authentication method properties and Remember Credentials checkbox

Notes:
EAP-MSCHAPv2 is a commonly used secured password authentication method.
Most EAP-based authentication methods require extra configuration provided through the “Configure” button.
For EAP-MSCHAPv2, the configuration is fairly simple. “Automatically use my Windows logon name and password” will use the currently logged on user. For a Windows Phone device, this might be the end-user’s private account that the phone was set up with (BYOD). The end-user would then enroll using their workplace credentials which would not be considered the logged in user. We suggest leaving that box unchecked so the end-user can provide their workplace credentials when prompted on their BYOD Windows Phone 8.1 device.
You can check “Remember the user credentials at each logon” so that the end-user will have their credentials saved once they have provided them for the initial VPN connection.
Wizard page 4: Configure proxy settings

Notes:
Proxy settings are optional. If your VPN connection / environment requires a proxy for the VPN connection then this is where you would configure it for your Window Phone 8.1 VPN profile.
Wizard page 4: Configure the DNS Suffix Search List

Notes:
Intune only supports the DNS Suffix search list setting for VPN profiles deployed to Windows Phone 8.1 devices. Each entry is a specific DNS suffix that will be searched when connecting to a website using a short name. For example: “http://MyWebSite” would be searched for as MyWebSite.contoso.com, MyWebSite.childdomain1.contoso.com, etc…)
Wizard page 5: Configure applicable platforms

Notes:
VPN profile deployment is supported on Windows Phone 8.1 and newer devices.
Split-tunneling option
Configure routes to enable Split-tunneling:
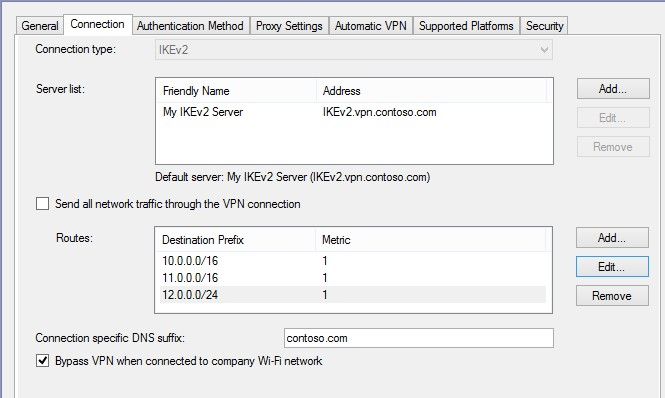
Notes:
“Send all network traffic…” box checked – enables force tunneling; unchecked - enables Split-tunneling
Routes will need to be set to tell the device when to use the VPN connection. If the network traffic has a destination that matches a Route/Destination Prefix, then the device will split that traffic onto the VPN connection. Any other traffic that does not match a route will not use the VPN connection.
All other wizard pages would be configured the same as above.
Smart-card or other Certificate option (EAP-TLS)
Configure EAP-TLS (cert-based) authentication

Notes:
“Smart Card or other certificate” is the EAP-TLS authentication method.
For the device to be able to find and use the correct certificate for the connection you need to configure EAP-TLS properties for your environment including the “Advanced” page.
Verifying the server’s identity is not required but is recommended.
Having the EKU set correctly with Client Authentication added under the “AnyPurpose” section is required.
All other wizard pages from above would be configured the same.
Deploying and monitoring a VPN Profile for Windows Phone 8.1
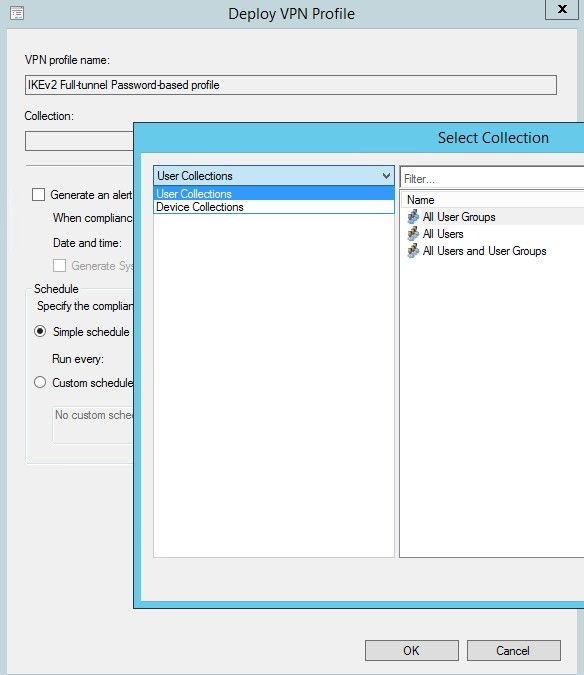
Deployment Wizard: Deploy to User or Device collection
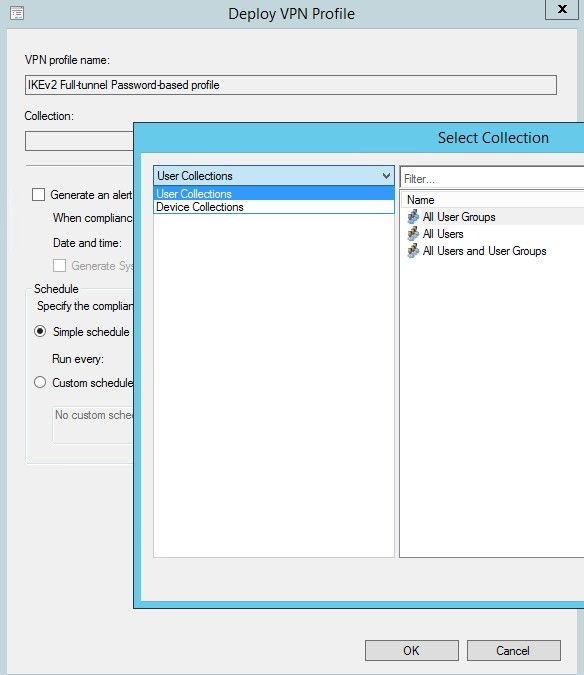
Notes:
We support deploying VPN profiles to User or Device collections.
You can configure an alert to be generated if compliance does not meet the SLA (Optional)
Schedule: This pertains to only the Windows on-premises client evaluation schedule. Windows Phone devices sync with the server and evaluate policies on their own schedule (default of every 8 hours).
Monitoring deployment of the VPN profile.
Compliant results look like this:

Error example:

Notes:
In this instance various settings failed to remediate. If these types of errors are seen then the suggested step would be to check the device for the profile. If only one setting reported failure that could just be due to a setting or value that is not supported by the Windows 8.1 device and the profile may have been placed on the device anyway. If you see various remediation errors like the example above then most likely the profile was not able to be placed on the device because of some issue with the device itself.
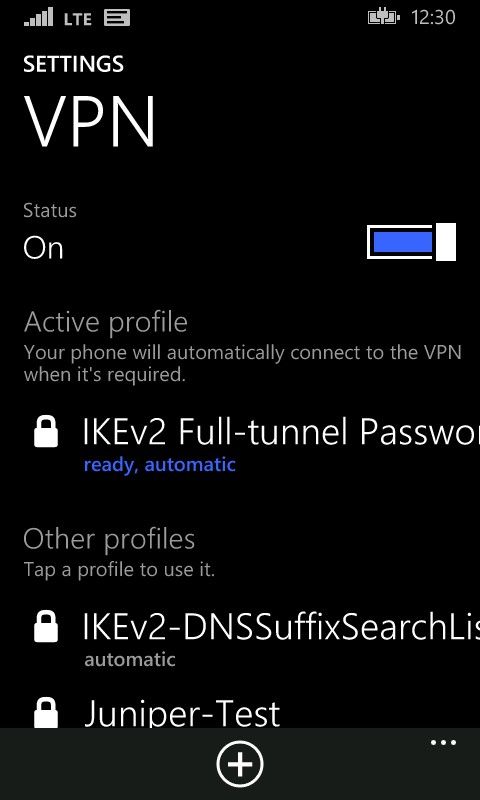
Checking the Window Phone 8.1 device for the profile:
You can find the VPN profiles under Settings -> VPN
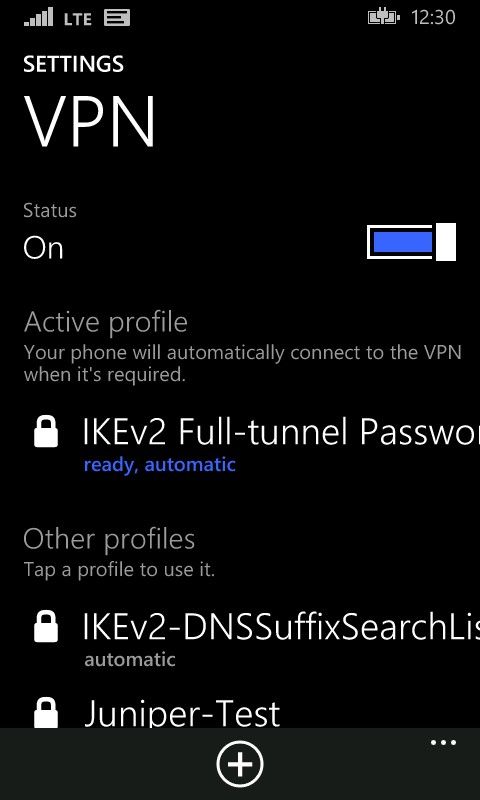
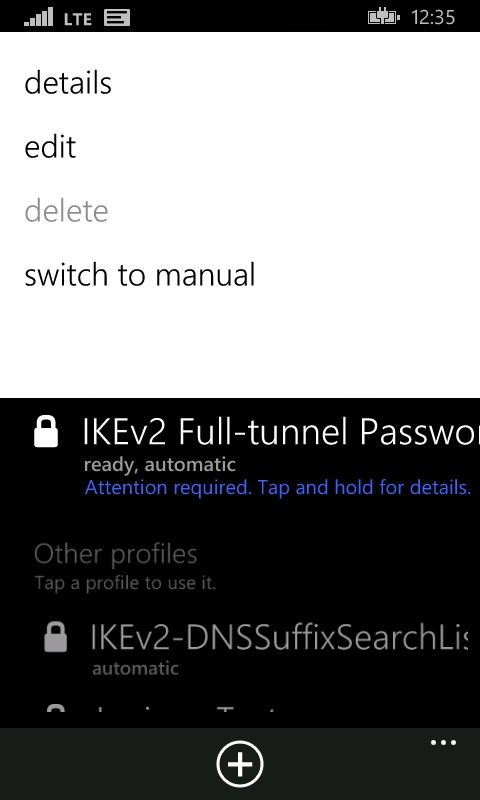
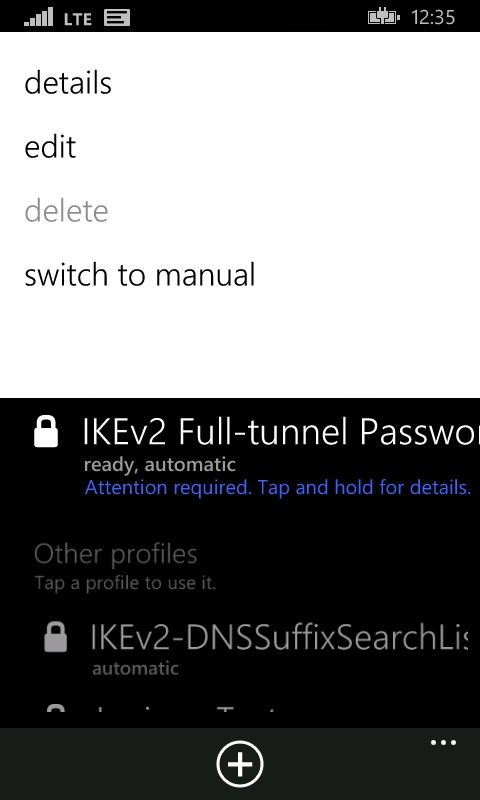
Notes:
The active profile is the one that will be connected or triggered. Tap a different profile to activate it. Tap and hold on a specific VPN profile to view details or edit its properties:

Summary
This document provides some examples of working IKEv2 VPN profile configuration. Of course every environment will be different and changes to the examples above would be needed but hopefully this information will guide you in the right direction.
Whenever in doubt, try creating the profile on the device manually to confirm that you understand how the profile should look in order to connect to your VPN server. If you cannot get your device to connect with a manually created profile then deploying a similar profile through the Configuration Manager console will likely not work either.
For more information about using VPN profiles in Configuration Manager, see VPN Profiles in Configuration Manager in the Configuration Manager Documentation Library .
--James Lieurance
Configuration Manager Resources
Documentation Library for System Center 2012 Configuration Manager
Configuration Manager 2012 Forums
System Center 2012 Configuration Manager Survival Guide
System Center Configuration Manager Support
This posting is provided "AS IS" with no warranties and confers no rights.
0
Likes