- Home
- Security, Compliance, and Identity
- Microsoft Entra Blog
- Azure Cloud App Discovery GA and our new Privileged Identity Management service
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Howdy folks, As SaaS apps and infrastructure in the cloud become increasingly important to our customers' businesses, we hear a lot of questions about new risks related to these critical resources. So today I'm really excited to share important news about how Azure AD can help you and your organization detect and manage risk related to access to cloud resources. First, our Cloud Application Discovery feature is now generally available, and with this release we have integrated it into the Azure preview portal. Cloud App Discovery helps you manage important risks related to "shadow IT." It gives you visibility into which SaaS apps your users are accessing, and helps you to prioritize which of these apps to bring under IT control. We have also just introduced an exciting preview of our new Privileged Identity Management feature, which helps you reduce risk from users that have permanent access to high-privilege roles. Now your admins can do most of their work as regular users, without elevated permissions. And when they need admin permissions to complete a high-privilege task, they can get those permissions using a "Just-In-Time" access feature that also removes the permissions after a pre-configured period of time. Cloud App Discovery is Generally Available Our Cloud App Discovery feature is now generally available to Azure AD Premium customers. With this release we have integrated Cloud App Discovery into the Azure preview portal, and have also enabled you to delegate access to Cloud App Discovery to users who are not global administrators. Cloud App Discovery enables you to:
- Discover cloud applications in use within your organization
- Identify which users in your organization are using an application
- Export data so you can analyze it offline in other tools
- Prioritize applications to bring under IT control, with single sign-on and user management.

Fig 1. Cloud App Discovery tile on the Startboard of the Azure preview portal
The first time you arrive at the Cloud App Discovery blade, click the Quickstart icon on the top of the blade. This provides guidance on how to get started with Cloud App Discovery, including how to download and deploy the agent, as well as details about how the feature works.

Fig 2: Cloud App Discovery Quickstart
Seeing your data on cloud applications usage Once you've installed the Cloud App Discovery agent on at least one client, you'll begin to see data on application usage in the Cloud App Discovery blades. The new blades expose all of the capabilities that the Cloud App Discovery feature had in preview. You can:- See the applications which were detected, and track application usage over time
- See the number of users using a particular application, and the identities of those users
- See the number of agents that are reporting data to the Cloud App Discovery service
- Sort applications by number of requests, volume of data, or the number of users using the application
- Control which applications to collect data on
- Export data to an offline store for custom analysis

Fig 3: Cloud App Discovery blades in Azure preview portal
Access Delegation By default, only the global administrators in your organization have access to the Cloud App Discovery feature. With this release, we've added access delegation to meet an important request articulated by many preview customers: Now you can grant access to the Cloud App Discovery feature to users who need it, such as users in the security organization, even if they're not global admins in your directory. To enable other users in your organization to use Cloud App Discovery, click on the Settings tile on the Cloud App Discovery blade. Then click "Manage Access." Then, select the users and groups in your directory that need access to the Cloud App Discovery feature.

Fig 4: Delegating access to the Cloud App Discovery Feature
To see a step-by-step walkthrough of the management experience in the Azure preview portal, and the installation of the Cloud Application Discovery agent, read our documentation here . Preview of Privileged Identity Management We've just turned on a preview of our Privileged Identity Management (Azure AD PIM) feature. This is an Azure AD Premium feature that improves your organization's cloud security posture by reducing risk from users who have access to highly-privileged roles, such as administrator roles in Azure AD and other services such as Office 365, Intune, and SaaS apps whose access is managed by Azure AD. No other cloud identity service offers this advanced capability. Overview Today, most admins have permanent and unmonitored permissions to high-value resources in order to do their jobs. While this is convenient, it poses major security concerns and makes their accounts high-value targets for security attacks. In many of the recent high-profile security breaches, a hacker found a way to compromise a user account that was permanently assigned to privileged roles. Then the attacker was able to use that account to access resources across the organization's network, in many cases going undetected for months. Many of our enterprise customers have told us they want to improve the security and reduce risk around access to these roles. Azure AD Privileged Identity Management reduces this risk by enabling you to:- Discover and monitor privileged roles . The Azure AD PIM Dashboard gives you visibility into and tracking of users with privileged roles.
- Automatically restrict the time that users have these privileged permissions through on-demand "just in time (JIT)" activation of permissions for pre-configured time windows.
- Monitor and track privileged operations for audit purposes or security incident forensics.
- Add stronger workflow gates for activation : Multi-Factor Authentication, human approval, and integration with ticketing systems
- Expanded management coverage for additional privileged roles and resources such as Office 365, Azure, & SaaS apps managed by Azure AD
- Expose APIs so you can to integrate your own workflow experiences.
- Click the Marketplace tile on your Startboard
- Click Security and Identity
- Click the 'Azure AD Privileged Identity Management' item indicated in the screenshot below
- Complete the wizard
- Pin the resulting service instance to your Startboard
- Click on the tile to get started with Azure AD Privileged Identity Management.
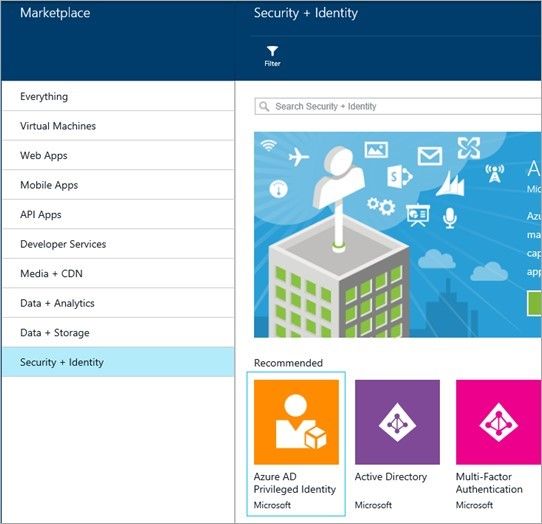
Fig 5: Privileged Identity Management item in the Marketplace of the Azure preview portal
Activate the security administrator role The first global administrator who initiates access to this preview is automatically assigned to the security administrator role, which is a new role used to manage privileged identities. Later you can add other users to the security administrator role. With Azure AD Privileged Identity Management, the basic model is that that a privileged role is assigned to candidate members, who in turn activate their membership in the role on-demand and for a limited pre-configured time. Since the security administrator role is a privileged role, in order to begin managing privileged identities you will need to activate your membership by clicking "Activate my role". You will see a list of roles assigned to you: the global administrator role with "permanent activation" and the new security administrator for which you need to "request activation". Finish the wizard to request activation for the security administrator role. During this preview, a user enters a business justification ("request reason") in the form of free text. While no meaningful validation is enforced today, the business justification it is logged and shows up in the audit experience along with the other details of the historical events. You can use it forensics or for detecting compliance issue with company policy, such as a policy that requires providing business justification like an incident number that needs privileged access to resolve. In future the business justification could be used for stronger validation by an authorization workflow.

Fig 6: Activating the security administrator role
Manage privileged identities The security administrator manages the other privileged identities. In the Privileged identities blade, you can see the privileged roles, including the security administrator role. For each privileged role, you can see how many users are assigned to that role, how many of these assignments are currently active and how many are permanently active. The table also shows a summary of the risk level in each role: If there are too many permanent assignments, it shows a yellow warning. If there are only a few permanent assignments, or none, it shows a green checkmark. You can configure the thresholds by right-clicking the row and editing the settings.
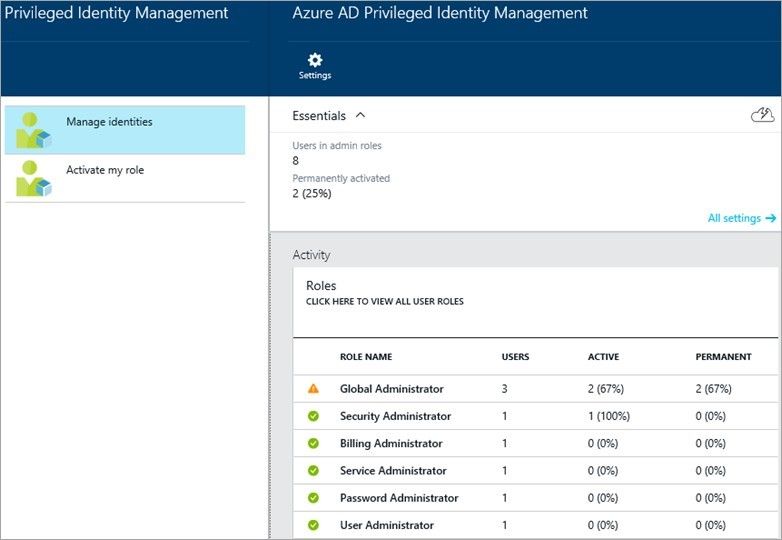
Fig 7: Managing privileged identities
You can click on the Roles tile to manage user assignments for privileged roles. You can view all privileged identities by role or name, add or remove users from privileged roles, make the assignments to privileged roles either temporary or permanent, or activate someone into their assigned privileged role, on their behalf. For example, you can assign an additional user to the security administrator role, either permanently or requiring temporary activation.

Fig 8: Managing an assignment to a privileged role
Click the Activation History tile to view detailed historical information regarding privileged roles. This includes operations done automatically by the service, such as expiring privileged roles at the end of the activation time window.

Fig 9: Viewing activation history of privileged roles
Self-service experience for administrators The privileged identities managed by Azure AD Privileged Identity Management are effectively regular users in the system until they are activated into their assigned privileged role. To activate their privileged role membership, a user:- Signs in to the Azure preview portal
- Adds the Privileged Identity Management tile to their Startboard by clicking on the Marketplace tile, selecting Security and Identity, and selecting the Azure AD Privileged Identity Management item. This is only required the first time the user accesses Privileged Identity Management functionality.
- Clicks the Privileged Identity Management tile to see the list of roles pre-assigned to them
- Activates their membership in a role by clicking "Make active"
- Provides business justification.

Fig 10: Requesting role activation
Azure AD Privileged Identity Management improves your ability to control and manage the highest security risks to your cloud identity infrastructure – your own privileged roles (administrators) -- that have become a high-value target for attackers. To see the user experience for the security admin to configure temporary access to a privileged role, and for a user to request activation into that role, see our video .As always, we're very interested in your feedback on these features. So if you have any questions or suggestions, just drop us a line in our forum .
Best Regards,
Alex Simons (Twitter: @Alex_A_Simons )
Director of Program Management
Microsoft Identity and Security Services Division
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.