Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Home
- Security, Compliance, and Identity
- Microsoft Entra Blog
- Learn all about the Azure AD B2B Collaboration Preview!
Learn all about the Azure AD B2B Collaboration Preview!
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Published
Sep 06 2018 08:26 PM
10.6K
Views
Sep 06 2018
08:26 PM
Sep 06 2018
08:26 PM
First published on CloudBlogs on Sep, 15 2015
Howdy folks, By now, hopefully you've already read my first blog post from today announcing the exciting news about the preview releases of Azure AD B2B and our Azure AD Collaboration features. This second post is a by Arvind Suthar, the Principal PM in our PM team who has lead our B2B efforts. I hope you'll find it interesting and give these new capabilities a try! And we'd love to receive any feedback or suggestions you have! Best Regards, Alex Simons (Twitter: @Alex_A_Simons ) ------------------------------ Hi there, I'm Arvind Suthar, a PM in the Identity Division at Microsoft. Today, I'm going to walk you through the new public preview of Azure AD B2B. This is a new set of capabilities that enable simple and secure collaboration with your business partners, providing a simple sign up process regardless of what kind of identity systems they have in place. Collaboration between organizations has become essential to the value companies create. Many companies take on projects that require partnering with other companies to spread risk or assemble expertise. Many companies, including Microsoft, have extensive supply chains and partner networks made up of large and small companies that are essential to delivering customer value. And identity and access management is at the core of each and every one these collaborations; you need to give your partners access to key applications and data, but you also need to make sure these assets don't end up in the hands of the wrong people. Traditionally, there have been two ways organizations have tried to solve this problem:
Howdy folks, By now, hopefully you've already read my first blog post from today announcing the exciting news about the preview releases of Azure AD B2B and our Azure AD Collaboration features. This second post is a by Arvind Suthar, the Principal PM in our PM team who has lead our B2B efforts. I hope you'll find it interesting and give these new capabilities a try! And we'd love to receive any feedback or suggestions you have! Best Regards, Alex Simons (Twitter: @Alex_A_Simons ) ------------------------------ Hi there, I'm Arvind Suthar, a PM in the Identity Division at Microsoft. Today, I'm going to walk you through the new public preview of Azure AD B2B. This is a new set of capabilities that enable simple and secure collaboration with your business partners, providing a simple sign up process regardless of what kind of identity systems they have in place. Collaboration between organizations has become essential to the value companies create. Many companies take on projects that require partnering with other companies to spread risk or assemble expertise. Many companies, including Microsoft, have extensive supply chains and partner networks made up of large and small companies that are essential to delivering customer value. And identity and access management is at the core of each and every one these collaborations; you need to give your partners access to key applications and data, but you also need to make sure these assets don't end up in the hands of the wrong people. Traditionally, there have been two ways organizations have tried to solve this problem:
- Inter-company federation relationships
- Internally managed partner identities
- Most large companies do business with many smaller companies that don't have the expertise and can't afford the server infrastructure to setup and manage federation.
- Complexity grows linearly when you have to manage a federation relationship with each partner. Managing thousands of federation relationships becomes untenable.
- With federation, you have very limited user level visibility making compliance and audit challenging.
- Accounts in these internally managed directories can easily provide too much access and put the whole organization at risk.
- These accounts are disconnected from the partner's identity system, so they are not disabled when partner employees change jobs or are terminated.
- This is yet another set of usernames and passwords for partners to remember and yet another set of identities for you to manage (provision, de-provision, reset passwords, etc.).
Introducing Azure AD B2B Collaboration
Azure Active Directory B2B collaboration lets you enable access to your corporate applications from partner managed identities. You can create cross-company relationships by inviting and authorizing users from partner companies to access your resources. Complexity is reduced as each company federates once with Azure AD and each user is represented by a single Azure AD account. Security is increased as access is lost when partner users are terminated from their organizations and unintended access is not granted by membership in internal directories. For business partners that don't already have Azure AD, B2B collaboration has a streamlined signup experience to provide Azure AD accounts to your business partners. Let's walk through Azure AD B2B from the admin and partner end user perspectives.Walkthrough: Admin Experience
B2B collaboration allows a company administrator to invite and authorize a set of external users by uploading a comma-separated values (CSV) file to the Azure management portal. The portal will send email invitations to these external users. The invited user will either sign in to an existing work account with Microsoft (managed in Azure AD), or get a new work account in Azure AD. Once signed in, the user will be redirected to the app that was shared with them.CSV file format
Azure AD B2B supports uploading a CSV file that contains information to brand the invitation and redemption experience and authorize access for the invited user.Uploading a CSV file
The Azure portal "Add User" dialog has been updated with a "Users in partner companies" option. The CSV file format as well as a sample CSV file are documented here .

Invitation Summary Report
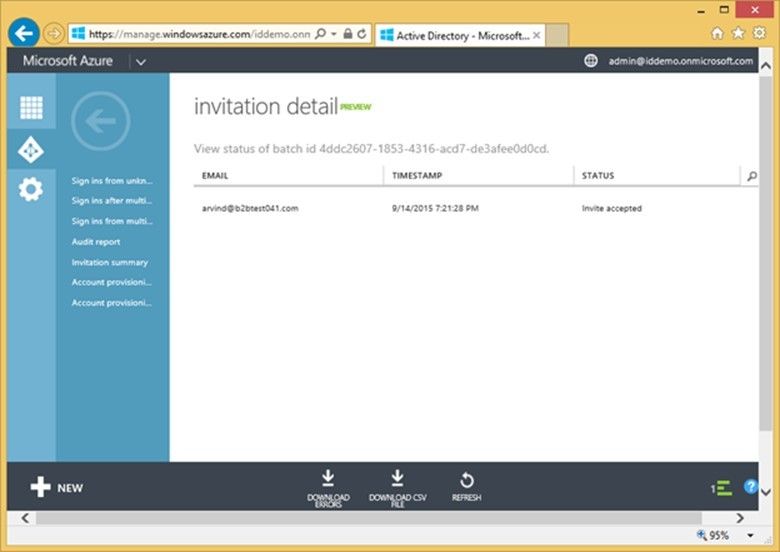
Once the CSV file is uploaded, the status of processed invitations can be reviewed in the "Invitation summary" report in the "Reports" tab of the inviting directory in the Azure management portal.Invitation Detail Report
Clicking on any Batch ID in the Invitation Summary report will launch an invitation detail report for that batch showing the email, processing timestamp, and status of each invited user. From this report you are able to download the errors in a CSV file that can be corrected and re-uploaded. You are also able to download the original CSV file from this page if needed.
Walkthrough: End User Experience
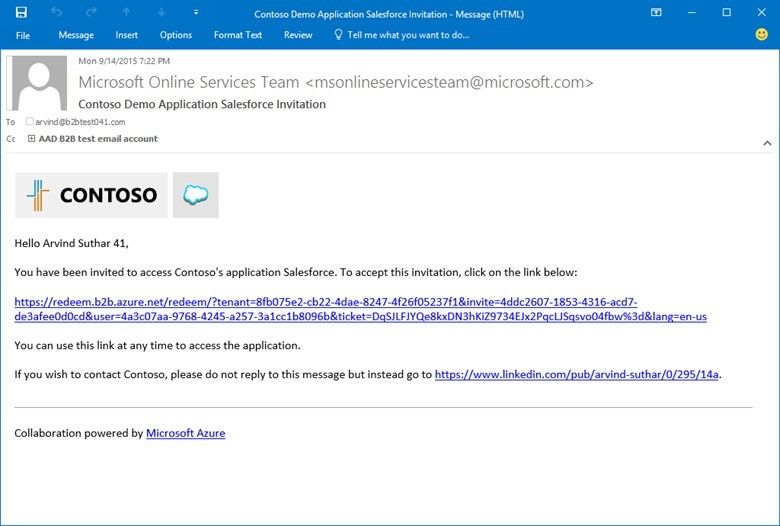
Invitation Email
The email that partner employees receive is branded with the tenant branding of the inviting organization and with the application branding of the application specified by the InviteAppID in the CSV. The user is prompted to go to the provided link to accept the invitation.
Invitation Accept Landing Page
The invitation accept landing page provides some context for the invited user on how to accept the invitation. The landing page below explains that the user is about to create an email verified account in Azure AD. The topic of email verified accounts and unmanaged tenants and how they can be brought under admin control are covered in this article on self-service signup. Under different scenarios, this landing page may explain that the user is about to sign in or that the user is signed in with a different account so needs to sign out first.

Simplified Signup for Partners Without Azure AD
When the user clicks "Accept" in the screen above, they get the Azure AD signup screen below prompting them to enter a password, display name, and region.



1 Comment
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.