Service Principal Names (SPN) for Dynamics NAV Web Services
We, the Microsoft Dynamics NAV Support Team in the Customer Service and Support (CSS) department, see from time to time cases asking for the Service Principal Names (SPN) that are required for Dynamics NAV Web Services (WS) to run properly on a three-tier environment with Kerberos enabled.
Let’s start with a little bit of history here:
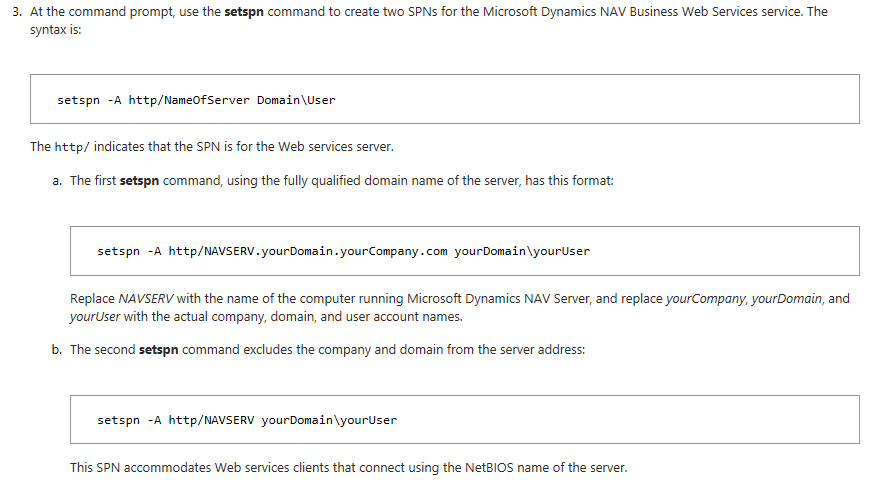
Back in Dynamics NAV 2009, when built-in NAV web services were introduced, documentation to follow when working on a three-tier environment (Delegation) was created and published to the MSDN Library:
How to: Configure Web Services with Delegation
Our colleague Scott Wright also wrote a clarification post at that time, where he went deeper in the issue, and it was published in this blog too:
NAV 2009 Web Services on a three machine setup
As you can see, in both cases port numbers were not included in the SPNs created, as Kerberos required them to be created just with FQDN and Netbios name of the machine where NAV service was running at for this purpose.
So far so good and everything was clear.
Then Dynamics NAV 2013 was launched, and we could see an improvement in this process:
SPNs were automatically created by the Service to the account of the user who was starting it and we also added HTPP SPNs with port number as we found some scenarios for NTLM where they were needed.
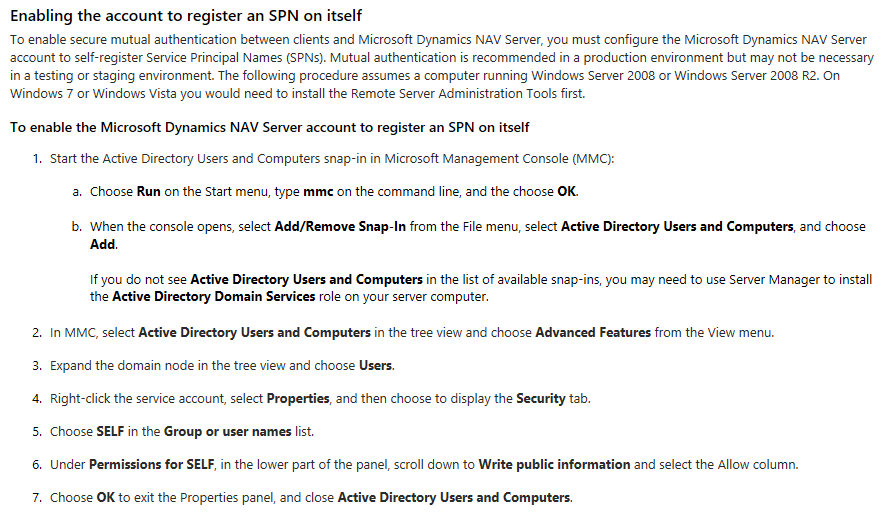
This was the reason why we had to enable the Dynamics NAV Server account to register an SPN on itself:
Provisioning the Microsoft Dynamics NAV Server Account
At this moment, both HTTP SPNs with Port Number (NTLM) and without Port Number (Kerberos) were created when the Dynamics NAV Server service was started so Kerberos protocol (The most restrictive one) was addressed.
However, we started receiving support requests stating that the creation of this HTTP SPNs without Port Number proactively had some duplication errors at some environments as a side effect, so we decided to launch a Hotfix in a Cumulative Update (CU) for Dynamics NAV 2013 R2 to stop creating HTTP SPNs without port number automatically:
Platform hotfix for Microsoft Dynamics NAV 2013 R2 (Build 35866)
This is the current situation for Dynamics NAV 2013 R2 and all later versions (Dynamics NAV 2015, Dynamics NAV 2016, Dynamics NAV 2017, and Dynamics NAV 2018).
Therefore, and as a summary:
- The Dynamics NAV Server service creates HTTP SPNs with Port Number whenever the service is started. This could be enough for installations where NTLM is enabled.
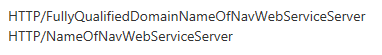
- If you require Kerberos authentication (the most restrictive one) you would need to add SPNs for HTTP without port number manually in this format:
I hope this helps clarifying this topic. Please share any feedback via comments. Also, keep an eye on the latest info on the Docs site.
Diego García Álvarez
Microsoft CSS EMEA
This posting is provided “AS IS” with no warranties, and confers no rights